How Australian organisations procure information technology has changed permanently. What was once...
What is spear phishing: A 2026 guide to defending against targeted attacks

First Published:
Content Written For:
Small & Medium Businesses
Large Organisations & Infrastructure
Government
Read Similar Articles
Have I Been Hacked? A Guide for Australian IT & Risk Leaders
That sinking feeling often starts with a single, urgent question: "Have I been hacked?" For...
Securing Video Conferencing Systems for Your Organisation
The rapid shift to hybrid work has transformed video conferencing systems from a simple...
Guide to ISO 31000 Risk Management in Australia
In the Australian threat environment, a purely reactive approach to risk is no longer a viable...
What Is Vishing? A Guide to Identifying Voice Scams
Vishing, a portmanteau of voice phishing, is a social engineering attack where criminals use the...
To understand what is spear phishing, think less of a wide net and more of a precision-guided weapon. Unlike generic phishing campaigns that blast thousands of users with identical, often easy-to-spot fakes, spear phishing is a highly targeted cyber attack. Furthermore, it is built on detailed reconnaissance to craft personalised and convincing emails aimed at specific individuals inside your organisation.
Defining the Threat for Security Leaders
Spear phishing represents a dangerous evolution in social engineering. It moves beyond broad, impersonal campaigns to execute precise, research-backed attacks that are far more difficult to defend against.
Attackers essentially become corporate spies. They leverage open-source intelligence from social media profiles, company websites, and even data breaches to learn the ins and outs of your business. Consequently, their goal is to gather specific details; project names, colleagues’ roles, or upcoming travel—to build a credible narrative that feels authentic.
This research allows them to convincingly impersonate a trusted person or entity, like a senior executive, a key supplier, or a government body. The resulting email appears legitimate because it contains context that only a real colleague or partner should know. This immediately establishes trust, which is the core mechanism that bypasses both technical defences and human suspicion. For Australian security leaders, understanding what is spear phishing is the first step in defending against it.
The core danger of spear phishing lies in its ability to weaponise trust. By mirroring legitimate business communications and exploiting established relationships, attackers trick even vigilant employees into making critical security errors.
Spear Phishing vs General Phishing Attacks
It is easy to confuse the two, but their methods and impact are worlds apart. While both use deceptive emails, spear phishing is a far more sophisticated and dangerous threat due to its tailored approach. The table below highlights the key distinctions.
| Attribute | General Phishing | Spear Phishing |
|---|---|---|
| Targeting | Broad, unfocused, targets thousands | Specific individuals or small groups |
| Personalisation | Generic greetings (“Dear Customer”) | Highly personalised using names, roles, projects |
| Reconnaissance | Minimal to none | Extensive research on the target and organisation |
| Lure | Common themes (password reset, lottery win) | Believable, context-rich business scenarios |
| Success Rate | Very low | Significantly higher due to credibility |
| Detection | Easier for filters to block based on volume | Difficult for automated systems to detect |
Ultimately, a general phishing attack is like a junk mail flyer left on every car in a carpark. In contrast, a spear phishing attack is like a registered letter addressed to you by name, referencing a recent conversation and asking for a specific action.
The Anatomy of Deception
The power of a spear phishing attack comes from its bespoke nature. For instance, an attacker might craft an email that appears to come from the CEO, referencing a recent all-hands meeting and asking the CFO to process an “urgent and confidential” invoice. The context makes the request plausible, overriding the recipient’s natural caution.
This tactic is particularly damaging for a few key reasons:
- High Success Rate: Because the lures are so specific and believable, their success rate is significantly higher than that of generic phishing attempts.
- Bypasses Standard Filters: Many spear phishing emails contain no malicious attachments or links in the initial message. Instead, they aim to start a conversation to build more trust before making the final move. This makes them incredibly difficult for standard email gateways to detect. For more insights, you can fortify your email security posture with our detailed guide.
- Primary Vector for Major Breaches: Spear phishing is a primary entry point for some of the most destructive cyber attacks, including Business Email Compromise (BEC) and ransomware deployment. Recent reports confirm that a huge percentage of breaches begin with the human element, often kicked off by a single, targeted email.
At its core, spear phishing is not just a technical problem; it is a human one. It exploits the inherent trust and urgency of professional environments, making it a persistent and top-tier threat for Australian organisations. Recognising this is fundamental to building a resilient defence.
The Anatomy of a Spear Phishing Attack
To build a solid defence against spear phishing, security leaders first need to understand the attacker’s playbook. Unlike the scattergun approach of regular phishing, a spear phishing campaign is a methodical, multi-stage operation. In short, it is a process that moves from intelligence gathering to final exploitation, built specifically to bypass both technical controls and human intuition.
The attack unfolds through careful reconnaissance, personalised lure creation, and a calculated delivery. This three-step process is what makes these attacks so dangerously effective.
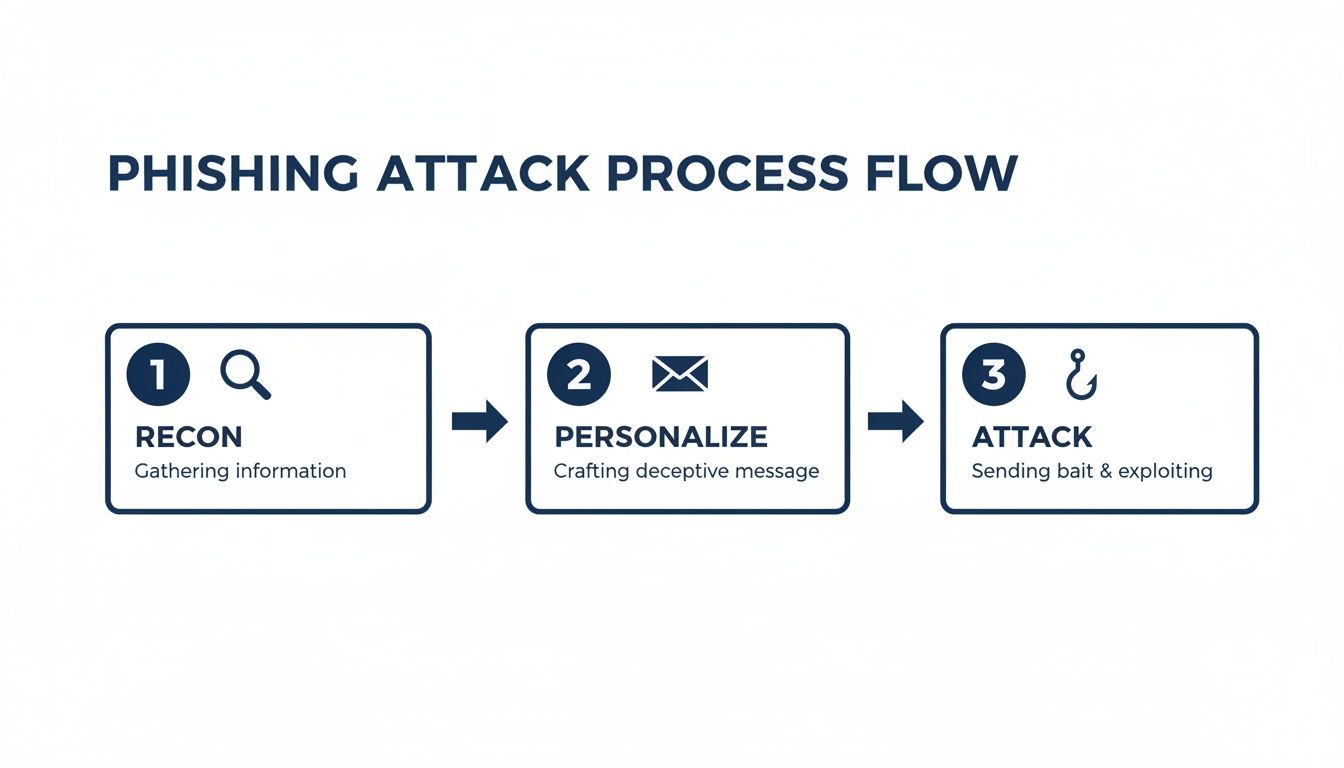
As you can see, the real work begins long before an email ever lands in an inbox. Attackers invest significant time and effort in the reconnaissance and personalisation stages, which is exactly why the final attack is so hard for a busy employee to spot.
Stage 1: Reconnaissance and Target Selection
A campaign always starts with extensive reconnaissance. Here, attackers use Open-Source Intelligence (OSINT) to build a detailed profile of their target organisation and, more importantly, its people. They become digital private investigators, trawling public information to find high-value individuals—usually executives, finance managers, or IT administrators with privileged access.
They pull this intelligence from a surprisingly wide range of sources:
- Company Websites: The ‘About Us’ page and staff directories are gold mines for names, job titles, and internal reporting structures.
- Social Media: Professional networks like LinkedIn give away connections, current projects, and even work-related travel schedules.
- Public Records and News: Press releases or news articles provide valuable context on recent company events, mergers, or major projects that can be used to add legitimacy.
This deep research allows attackers to pinpoint targets whose compromise will deliver the biggest payoff, whether that is direct financial theft or a foothold to access critical systems. Using cyber security threat intelligence is one of the few ways organisations can get ahead of these reconnaissance efforts.
Stage 2: Lure Crafting and Pretext Development
Once a target is selected, the attacker moves on to crafting the lure. This is where they build a believable pretext—a fabricated but plausible scenario to justify their request. This pretext is the heart of the social engineering effort and is constructed entirely from the intelligence gathered in stage one.
Common pretexts we see time and again include:
- Executive Impersonation: An email that looks like it’s from the CEO, asking for an urgent wire transfer to a “new vendor” ahead of an announcement.
- Supplier Forgery: A message appearing to come from a known supplier, attaching an updated invoice that just so happens to have new bank details.
- IT Department Spoof: A notification asking the user to log into a “new portal” to update their credentials or security settings.
The email itself is meticulously personalised. It will use the target’s name, reference their specific role, mention real colleagues, and allude to genuine company projects. This level of detail makes the message feel legitimate, disarming suspicion and creating a powerful sense of urgency or obligation.
Stage 3: Delivery and Post-Breach Actions
The final stage is the attack itself: delivering the malicious email and executing the plan once the hook is set. The ‘hook’ is the specific action the attacker wants the target to take, whether that is clicking a malicious link, opening a weaponised attachment, or replying with sensitive data.
Once the target takes the bait, the breach unfolds quickly:
- Initial Compromise: A malicious link sends the user to a credential harvesting page designed to be a pixel-perfect replica of a legitimate login portal (like Microsoft 365), capturing their username and password.
- Credential Theft: The attacker immediately uses the stolen credentials to gain their first foothold in the corporate network or a cloud environment.
- Lateral Movement: From there, the attacker moves quietly across the network, looking for ways to escalate their privileges and find more valuable systems and data.
- Objective Execution: The final goal is achieved. This could be anything from deploying ransomware and exfiltrating intellectual property to executing fraudulent financial transactions.
Spear phishing is not just an evolution of traditional phishing; it is a highly targeted and devastating tactic. Here in Australia, the 2019 Australian National University (ANU) data breach showed just how much damage it can cause. Cybercriminals used several spear-phishing campaigns to compromise a senior staff member’s email, giving them access to the university’s core systems. Ultimately, the attack exposed the personal details, tax file numbers, and payroll information of over 200,000 people, making it one of the largest breaches in Australian higher education history.
The Australian Spear Phishing Threat Landscape
For Australian security leaders, understanding the mechanics of spear phishing is only half the battle. The threat is not theoretical; it is a clear and present danger actively targeting our businesses, exploiting our unique commercial culture, and costing the economy billions each year. Indeed, high-profile breaches show attackers are masters at tailoring their campaigns to resonate with local events and business norms.
This precision makes spear phishing the primary vector for major cyber incidents across the country. Attackers use it as the initial entry point for far more damaging attacks, including Business Email Compromise (BEC) and crippling ransomware deployments. Consequently, the consequences are real and severe, leading to direct financial loss, operational chaos, and significant reputational damage that can take years to repair.
High-Profile Australian Breaches
Real-world examples move the discussion from abstract risk to concrete business reality. They show just how quickly a single, well-crafted email can unravel an organisation’s defences.
The 2020 Service NSW data breach is a textbook case. In this attack, cybercriminals sent highly targeted spear phishing emails to just 47 staff members. The compromise of those accounts gave attackers access to an email inbox containing an astonishing 5 million sensitive documents, ultimately exposing the personal data of approximately 104,000 individuals. The incident is a stark reminder of how attackers exploit trusted internal communication channels to achieve a massive data payload.
Spear phishing works so well in Australia because it bypasses technical defences by targeting the human element. Attackers weaponise trust and urgency, turning an employee’s instinct to be helpful into a critical security vulnerability.
Quantifying the Local Impact
Statistics from Australian authorities paint a grim picture of the financial and operational toll. The Australian Cyber Security Centre (ACSC) consistently reports that spear phishing is a key facilitator of costly cybercrime. These attacks are not just a nuisance; they are a direct threat to the bottom line of Australian enterprises.
The data shows that spear phishing has fuelled a surge in both business email compromise (BEC) and ransomware incidents. For example, the ACSC responded to 138 ransomware incidents in a recent financial year, with 39% of these triggered by initial warnings of a breach—which often start with a targeted phish. In Australia and New Zealand, large enterprises face a concerning 44.6% Phish-prone Percentage (PPP), while medium-sized firms are not far behind at 29.2%.
The Rise of AI-Powered Attacks
The threat is becoming even more complex as attackers integrate artificial intelligence into their attack methods. AI is now used to generate hyper-realistic spear phishing emails at an unprecedented scale and speed, presenting a formidable challenge for both human and technical detection.
What does this mean for your organisation?
- Flawless Language and Tone: AI-powered tools can eliminate the spelling and grammatical errors that were once tell-tale signs of phishing, producing perfectly crafted messages.
- Hyper-Personalisation at Scale: Attackers can use AI to rapidly analyse open-source intelligence, generating thousands of unique, personalised emails tailored to individual targets.
- Mimicking Communication Styles: Advanced models can even learn and replicate the specific communication style and jargon used within your organisation, making impersonation attempts almost indistinguishable from genuine emails.
This technological shift makes it more critical than ever for Australian organisations to look beyond traditional defences. The latest trends are covered in depth in the official ASD Cyber Threat Report, which provides crucial context for security leaders. As attackers’ tools become more advanced, our defensive strategies must evolve to keep pace, focusing on building a resilient and security-aware culture.
Building a Multi-Layered Defense Strategy

Understanding the anatomy of a spear phishing attack is only half the battle. The real work begins when you start building your defences. For Australian organisations, this means getting serious about a multi-layered security posture that moves far beyond a single line of protection.
A successful strategy weaves together strong technical controls with an equally resilient human firewall. This integrated approach is the only way to effectively counter today’s highly personalised and psychologically manipulative attacks.
Fortifying Your Technical Defences
No single piece of technology can stop every spear phishing attempt. Your primary goal is to make it as difficult as possible for a malicious email to even reach an employee’s inbox. This requires a modern email security stack, not just a basic spam filter.
Key technical controls should include:
- Advanced Email Security Gateways: Your gateway needs sophisticated anti-impersonation and anti-spoofing capabilities. These systems are designed to analyse sender behaviour, domain reputation, and email headers to spot Business Email Compromise (BEC) attempts and brand impersonation before they cause damage.
- Full DMARC Implementation: Setting DMARC (Domain-based Message Authentication, Reporting, and Conformance) to a
p=rejectpolicy is a non-negotiable step. It prevents attackers from directly spoofing your domain, making it much harder for them to successfully impersonate your executives or brand. - Endpoint Detection and Response (EDR): You must assume that eventually, someone will click. EDR solutions offer crucial visibility after the initial compromise, monitoring for unusual processes, network connections, or other signs of malicious activity on the endpoint. This allows your team to contain threats before they escalate into a full-blown breach.
Together, these technologies filter the obvious threats, validate sender identities, and give you a fighting chance to catch malicious activity that slips through the net.
Strengthening the Human Layer
Technology on its own is never a complete answer to what is spear phishing defence. Because these attacks are designed to exploit human trust and psychology, your employees must become your most active line of defence, not your weakest link.
This requires a move away from the generic, once-a-year compliance training that simply ticks a box.
A crucial layer of any defence is robust employee education. Understanding how to implement effective training in compliance can significantly bolster your team’s ability to recognise and report suspicious activities.
A modern approach focuses on continuous education and realistic simulation to drive real behavioural change:
- Measure Your Phish-prone Percentage (PPP): You cannot manage what you do not measure. Regular, realistic spear phishing simulations that mimic real-world attacks will give you a clear PPP metric, showing you exactly what percentage of your team is vulnerable.
- Drive Behavioural Change: Use the results from your simulations to deliver immediate, just-in-time training to employees who click. This approach directly connects the mistake with the lesson, making it far more memorable and effective than a generic training module a month later.
- Foster a Reporting Culture: Make it dead simple for your staff to report a suspicious email with a single click. A strong reporting culture turns every employee into a sensor for your security team, providing invaluable, real-time threat intelligence.
For a deeper dive, our guide on security awareness training for Australian organisations offers actionable strategies to build this human firewall.
Aligning Defence with Australian Compliance
Finally, your defensive strategy must be aligned with established Australian compliance frameworks. This not only improves your security posture but also ensures you meet both regulatory and customer expectations. For local businesses, that means mapping controls to the ASD Essential 8 and ISO 27001.
- ASD Essential 8: Core measures like application control, restricting admin privileges, and multi-factor authentication are all crucial for limiting the damage a successful spear phishing attack can cause.
- ISO 27001: The controls in Annex A, particularly around access control (A.9), communications security (A.13), and supplier relationships (A.15), provide a structured and internationally recognised framework for building out your defences.
The role of spear phishing in Australia’s data breach landscape is stark. With 37 million unique Australian email identifiers compromised since 2004 and breaches skyrocketing 388% in Q1 2026, the threat is undeniable. Given that Phish-prone Percentages in large ANZ firms sit at 44.6%, the need for a truly multi-layered approach has never been more urgent.
Your Incident Response Plan for a Breach

Even with strong defences, the reality for Australian organisations is that a sophisticated spear phishing attack will eventually succeed. When that day comes, how your team reacts in the first few hours is what matters most. A panicked, disorganised response only amplifies the damage. In contrast, a structured, well-rehearsed incident response (IR) plan allows you to seize control and protect the business.
This is not some complex document that sits on a shelf. It needs to be a practical playbook your team can execute under immense pressure. For a spear phishing incident, that playbook is built around four core stages: Identify, Contain, Eradicate, and Recover. Executing these steps decisively connects the technical response with crucial commercial and legal decisions.
Identify The Breach
The moment a potential compromise is flagged—whether from an employee reporting a suspicious email or an EDR alert—the clock starts ticking. The goal here is to confirm if a breach has actually happened and, if so, understand its initial scope. Rushing this can destroy crucial evidence.
Your team needs to move quickly but methodically, answering a few key questions:
- Was the user account compromised? Look for tell-tale signs like logins from unusual locations, unexpected MFA push notifications, or new email forwarding rules.
- Was the endpoint compromised? Analyse the device for malware, unauthorised remote access tools, or signs of an attacker trying to move laterally.
- What was the entry point? Preserve the original spear phishing email. Analyse its headers and content to figure out the lure and how it was delivered.
This initial analysis is the foundation for the next, most critical stage: containment.
Contain The Intrusion
Containment is all about stopping the bleeding. Your immediate priority is to sever the attacker’s access and stop them from burrowing deeper into your network. A successful spear phishing attack gives them a foothold; containment traps the attacker on that initial beachhead.
Actions in this phase need to be swift and decisive:
- Isolate Compromised Systems: Immediately disconnect any affected endpoints from the network. You can do this by physically unplugging the network cable or using your EDR tool to quarantine the device.
- Disable Compromised Accounts: Instantly reset passwords and, just as importantly, revoke all active sessions for the user accounts involved. This locks the attacker out of email, cloud apps, and internal systems.
- Block Malicious Infrastructure: Use your firewall and web filter to block any domains, URLs, or IP addresses you identified during the analysis. This cuts off command-and-control communication.
A critical part of mitigating the damage from a spear phishing attack is having a robust and well-defined incident response plan. You can learn more about the specific requirements for an incident response plan in the context of security compliance.
Eradicate And Recover
Once the threat is contained, the focus shifts to methodically removing every trace of the attacker from your environment. This goes far beyond just deleting a malicious file. It means ensuring every backdoor, malicious script, and persistence mechanism is found and eliminated.
Only then can you move to the recovery phase, which focuses on securely restoring systems to normal operation. This means rebuilding compromised systems from a known-good state—never try to just clean them. After eradication, you can begin restoring data from clean backups and carefully re-enabling services. Every step must be documented for post-incident reviews and potential regulatory reporting.
For a detailed walkthrough, our guide to building a computer incident response plan offers further guidance.
Address Your Regulatory Obligations
For Australian organisations, the technical response is only half the story. A successful attack that leads to a data breach triggers significant legal and commercial responsibilities.
You must assess whether the incident meets the criteria for mandatory reporting under Australia’s Notifiable Data Breaches (NDB) scheme. If personal information was accessed and is likely to result in serious harm, you have a legal duty to notify the Office of the Australian Information Commissioner (OAIC) and affected individuals.
Failing to report can lead to severe financial penalties and serious reputational damage. This step is an essential part of managing the aftermath of any significant security event, especially one originating from a targeted attack like spear phishing.
Frequently Asked Questions About Spear Phishing
Even with strong defences in place, IT leaders still have practical questions about how spear phishing plays out in the real world. This section answers the most common queries we hear from Australian CISOs and IT managers, reinforcing what it takes to build a genuinely resilient organisation.
How Can We Identify a Spear Phishing Email If It Looks So Convincing?
Even the most sophisticated spear phishing emails contain subtle giveaways. Train your team to scrutinise the sender’s email address for tiny, almost unnoticeable variations and to hover over every link to check the destination URL before they click.
Your strongest defence, though, is a culture of healthy scepticism. Staff must feel empowered to verify unexpected requests for credentials, data, or payments through a separate channel, like a direct phone call. Simple technical controls also provide a powerful visual cue, like an email banner that clearly flags all messages coming from external senders.
Is Our Advanced Email Filter Enough to Stop Spear Phishing?
While an advanced email security gateway is a critical first line of defence, it is not a silver bullet. The whole point of spear phishing is to bypass these filters using sophisticated social engineering, clever impersonation, and emails that do not contain any malicious payload.
Because these attacks often lack obvious red flags like malware attachments, they can easily slip through automated checks. A multi-layered strategy is non-negotiable for anyone serious about understanding what is spear phishing defence. You must combine your technical filters with continuous, realistic security awareness training and a simple, one-click process for employees to report suspicious emails to your security team.
What Is the First Step After Discovering a Spear Phishing Attack?
Your first and most critical priority is containment. The very first action should be to isolate any compromised devices from the network. This stops the attack from spreading laterally across your environment.
At the same time, you need to disable the affected user accounts immediately to revoke the attacker’s access to email, cloud applications, and internal systems. It is also vital to preserve all evidence—like the original email and system logs—for forensic analysis. A pre-prepared incident response plan will guide the next steps of eradication and recovery, while you assess the breach scope to determine your obligations under Australia’s Notifiable Data Breaches (NDB) scheme.
At CyberPulse, we provide Australian organisations with the expert guidance and advanced managed services needed to build a resilient defence against targeted threats. From realistic phishing simulations to 24/7 managed detection and response, we help you shift from reactive fixes to a proactive security posture. Secure your organisation with CyberPulse.
Browse to Read Our Most Recent Articles & Blogs
Subscribe for Early Access to Our Latest Articles & Resources
Connect with us on Social Media

