How Australian organisations procure information technology has changed permanently. What was once...
What Is Vishing? A Guide to Identifying Voice Scams

First Published:
Content Written For:
Small & Medium Businesses
Large Organisations & Infrastructure
Government
Read Similar Articles
Have I Been Hacked? A Guide for Australian IT & Risk Leaders
That sinking feeling often starts with a single, urgent question: "Have I been hacked?" For...
Securing Video Conferencing Systems for Your Organisation
The rapid shift to hybrid work has transformed video conferencing systems from a simple...
Guide to ISO 31000 Risk Management in Australia
In the Australian threat environment, a purely reactive approach to risk is no longer a viable...
What is spear phishing: A 2026 guide to defending against targeted attacks
To understand what is spear phishing, think less of a wide net and more of a precision-guided...
Vishing, a portmanteau of voice phishing, is a social engineering attack where criminals use the telephone to trick employees into divulging sensitive information or performing actions that compromise organisational security. Unlike phishing emails, what is vishing relies on exploiting human trust directly over a call. Consequently, it bypasses technical defences by targeting a person, making it a powerful and growing threat for Australian organisations.
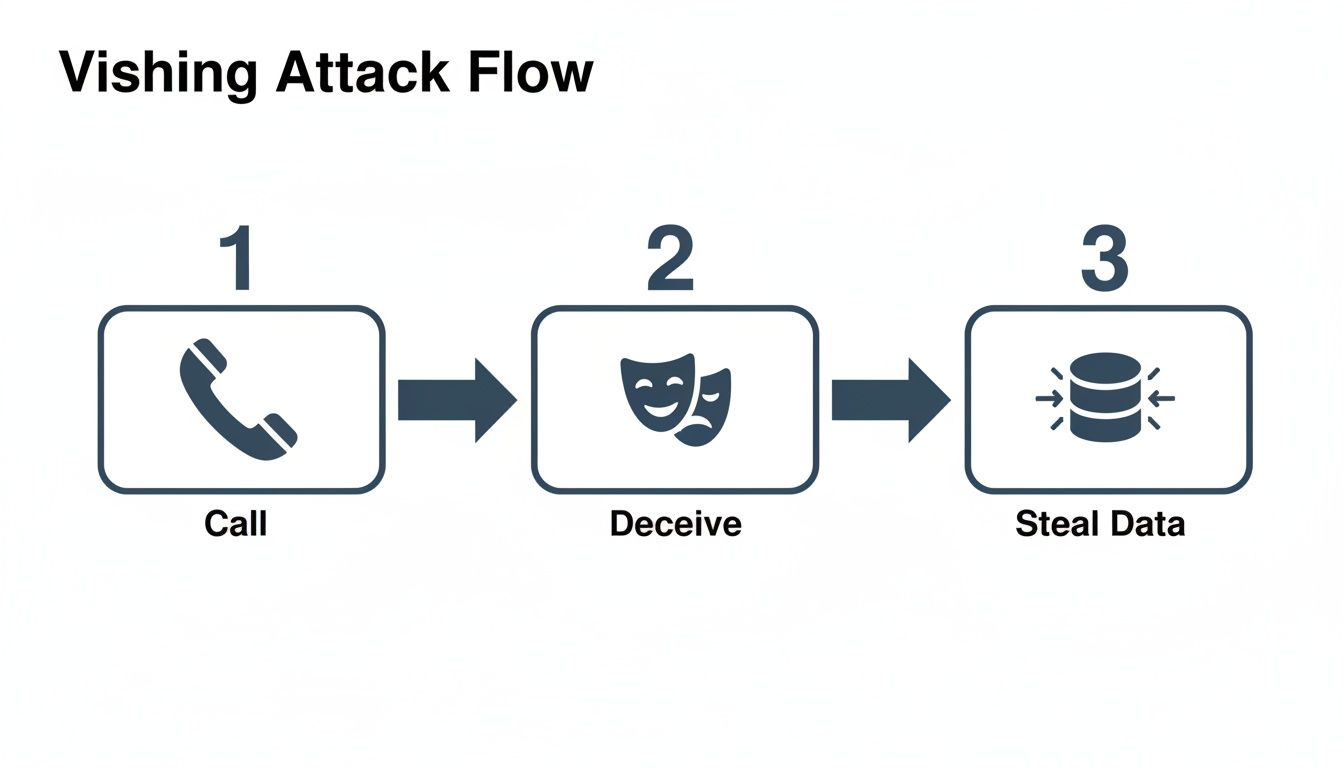
Before we dive deeper, here’s a quick overview of what a vishing attack involves.
Vishing Attack At A Glance
| Component | Description |
|---|---|
| Vector | Live phone calls, VoIP services, or automated voice messages (robocalls). |
| Tactic | Social engineering that relies on impersonation, urgency, and authority. |
| Target | Employees with access to sensitive systems, data, or financial accounts. |
| Goal | To steal credentials, gain remote access, or initiate fraudulent transactions. |
These attacks are effective because they create a sense of immediate pressure that a simple email cannot replicate, pushing people to act before they can think.
Decoding the Anatomy of a Vishing Attack
Imagine a con artist who wants to get into your secure server room. Instead of trying to breach the reinforced walls or disable the alarms, they just call reception. Posing as a trusted vendor with an urgent problem, they convince your staff to let them walk right in. This is exactly how vishing works. In short, it sidesteps firewalls and filters by targeting the one asset no software can patch: human psychology.
Attackers use a mix of impersonation, manufactured urgency, and a false sense of authority to pressure employees into making mistakes. For example, they might pretend to be an IT technician from your managed service provider, a senior executive needing immediate help, or even an official from the Australian Taxation Office (ATO) threatening penalties.
The goal is to create a high-stakes scenario where the employee feels they have no choice but to bypass normal procedures. This might mean divulging their login details, authorising a fake payment, or granting the attacker remote access to their computer. Therefore, the personal, real-time nature of a phone call makes it a dangerously effective tactic.
Vishing represents a critical shift in the threat landscape. Attackers are moving away from easily filtered malicious emails and are instead investing in voice-based deception that preys on ingrained human responses to authority and urgency, making it a severe business risk.
The Alarming Rise in Australian Vishing Operations
This is not a theoretical problem; it is a clear and present danger to Australian businesses. The personal nature of these calls makes them incredibly convincing, often leading to huge financial and reputational damage. Furthermore, recent data shows a dramatic spike in these attacks, highlighting a clear pivot by criminals towards this method.
The Australian government’s own reporting validates this trend, with social engineering tactics frequently appearing in major security incidents. You can learn more about the broader context in our analysis of the ASD Cyber Threat Report 2025. This kind of insight is crucial for CIOs and CISOs, especially in heavily regulated sectors like finance, healthcare, and education, where the fallout from a breach goes far beyond just financial loss.
To get in front of vishing, Australian organisations first need to understand the attacker’s playbook. A vishing attack is not some random, opportunistic phone call. It is a calculated operation that follows a predictable, three-stage sequence.
Think of it as a social engineering heist. The target is not a bank vault, but your organisation’s sensitive data, system access, and financial assets. By breaking down this process, you can spot the critical points where you can intervene and build stronger, more resilient defences.
Stage 1: Reconnaissance and Targeting
The first phase happens in the shadows, long before anyone picks up a phone. Attackers do their homework, gathering intelligence on your organisation to pinpoint high-value targets. They trawl public sources like your company website, LinkedIn profiles, and industry directories to map out your structure.
Their goal is to find employees in very specific roles, such as:
- Finance and Accounts Payable: Staff who can authorise payments or update supplier banking details.
- Executive Assistants: Individuals managing schedules and communications for senior leaders.
- IT Helpdesk and System Administrators: People with privileged access to critical systems and user accounts.
- New Hires: Employees who are often less familiar with security protocols and keen to be helpful.
This intelligence is what makes the scam so believable. The attacker will know managers’ names, the software you use, and maybe even recent company news. It all adds a layer of legitimacy to their story. This preparation is a key part of understanding what is vishing at a strategic level. For a deeper look into how attackers gather and use such information, see our guide on cyber security threat intelligence.
Stage 2: Execution and Deception
With a target selected and their script perfected, the attacker makes the call. This is where technology and psychology combine to create a powerful deception. Attackers often use Voice over IP (VoIP) technology with Caller ID spoofing to make the call look like it is coming from a legitimate source, like your own IT department or a trusted supplier.
This simple flow shows how the attack works in practice.
The deception is all about social engineering. The attacker uses a range of psychological triggers to build trust and then exploit it to steal critical assets.
The core of a vishing attack is the manipulation of trust. Attackers create a scenario where defying their request seems riskier or more difficult than complying. They exploit our natural inclination to be helpful and to respect authority.
Some of the most common scripts we see include:
- The IT Support Scam: Posing as a helpdesk technician, the attacker claims there is an urgent problem with the employee’s account. They then instruct the target to install remote access software or give up their login credentials to “fix” the non-existent issue.
- The CEO Fraud: The attacker impersonates a senior executive, often claiming to be in a meeting or travelling and needing an urgent, confidential wire transfer. They use authority and urgency to pressure the employee into bypassing financial controls.
- The Supplier Invoice Fraud: The visher pretends to be from a known supplier, claiming their bank details have changed. They then provide a new account number for the next payment, diverting your funds directly into their own pockets.
Stage 3: Exploitation and Monetisation
Once the attacker has tricked the employee, the final stage begins. The goal here is simple: to exploit the access or information they have gained for financial profit or to dig deeper into your network.
If they have stolen credentials, they will immediately try to access corporate accounts, email, and sensitive databases. If they convinced an employee to install a Remote Access Trojan (RAT), they will use it to create a persistent backdoor into your network, escalate privileges, and quietly exfiltrate data over time.
In payment fraud scenarios, the monetisation is instant. Understanding this full lifecycle is the first step for any organisation looking to disrupt these increasingly costly attacks.
How to Recognise the Red Flags of Vishing

To effectively counter vishing, every employee needs to become a confident first line of defence. This means arming them with the practical skills to spot a fraudulent call as it happens. Much like a bank teller learns to identify counterfeit money, your team can be trained to recognise the subtle but consistent red flags of a vishing attack.
The goal is to move beyond simply knowing what is vishing and start building real-world recognition skills. Attackers use a well-worn playbook of psychological triggers to bypass rational thought and provoke an immediate, emotional response. By understanding this playbook, your staff can learn to question, verify, and report suspicious calls before any harm is done.
Psychological Red Flags and Manipulative Language
Vishing attackers are social engineers. They use specific language and emotional pressure to get what they want. In fact, the phone call itself is their weapon, designed to short-circuit critical thinking. Your team should be trained to become instantly sceptical if they hear any of these tactics.
-
Manufactured Urgency: The caller creates a fake crisis demanding immediate action. For instance, they’ll say things like, “Your account will be suspended in five minutes unless you verify your details,” or, “This invoice must be paid immediately to avoid service interruption.” This pressure is designed to make the target panic and act without thinking.
-
Threats of Dire Consequences: This tactic goes hand-in-hand with urgency and involves threats of legal action, financial penalties, or even job loss. An attacker posing as an ATO official might threaten audits and fines, while someone impersonating a senior manager could imply career repercussions for not complying.
-
Deviation from Established Procedures: Any request that sidesteps your standard operating procedures is a major red flag. Be cautious of phrases like, “I know we normally need a PO, but can you process it just this once?” or, “Can you just read me your password so I can fix this quickly?” These are classic signs of an attempt to subvert security controls.
Technical and Contextual Warning Signs
Beyond the psychological games, there are often technical and contextual clues that can expose a vishing attempt. While attackers use technology like Caller ID spoofing to look legitimate, other parts of the call can reveal them.
Vishing calls often betray themselves through a combination of inconsistent details and a pressured atmosphere. If the call feels ‘off’—whether it’s the sound quality, the caller’s knowledge, or the nature of the request—it almost certainly is. Trusting that instinct and verifying the request through a separate, known channel is the most effective defence.
The scale of this problem is reflected in official Australian cybercrime statistics. Over the past year, the Australian Cyber Security Hotline received an average of 116 calls daily, with nearly 85,000 cybercrime reports filed annually.
Here are some technical and environmental red flags to watch for:
- Poor Call Quality or Strange Background Noises: Illegitimate calls often come from overseas call centres, even if the Caller ID looks local. Unexplained background noise, odd delays, or a poor connection can all be warning signs.
- Requests for Sensitive Information: A legitimate organisation—especially your bank or internal IT department—will never call you and ask for your full password, a multi-factor authentication (MFA) code, or your credit card details over the phone.
- Vague or Generic Details: While attackers do their homework, their knowledge is often shallow. A caller using generic terms like “your system” instead of a specific software name, or someone who cannot verify their identity with information only a real colleague would know, is highly suspicious.
Ultimately, building a robust human firewall is the most powerful control against these attacks. For more strategies on this, check out our guide on security awareness training for Australian organisations.
Calculating the True Cost of a Vishing Breach
When a vishing attack hits, the fraudulent transaction is just the beginning. For Australian CIOs and CISOs, the real task is grasping the full commercial fallout, because that is what justifies proactive security spending. Indeed, a single successful call can kick off a chain reaction of hidden costs that make the initial theft look minor, causing serious financial and operational pain long after the phone is hung up.
Think of it like this: the direct fraud is the impact, but the clean-up is where the real costs multiply. These secondary expenses escalate quickly, turning what might seem like a small security slip into a major business crisis that hits everything from your brand to your regulatory standing.
The Hidden Financial Drain Beyond Direct Fraud
The moment a breach is confirmed, a whole internal emergency response spins up, and it’s expensive. This is not just about clawing back one payment. It is a full-scale effort that pulls people and resources away from their real jobs. Consequently, adding up these expenses shows you the true cost of not being prepared.
Key post-breach costs almost always include:
- Incident Response and Forensics: Getting internal teams or external experts to dig into the breach, figure out how bad it is, and kick the attacker out of your systems. This means a lot of man-hours and specialist invoices.
- System and Data Recovery: The cost to restore systems from backups, check that your data is still intact, and make sure no malicious software is left behind. This can cause operational downtime, which directly hurts revenue.
- Legal and Notification Expenses: Bringing in lawyers to handle complex breach notification rules and communicating with customers, partners, and regulators. This gets particularly expensive if any customer data was involved.
A vishing breach isn’t just a financial event; it’s an operational one. The true cost lies in the extensive effort required to investigate, remediate, and recover, all while managing the significant reputational and regulatory fallout.
Navigating the Regulatory Minefield
For Australian organisations, particularly those in regulated industries, the consequences of a vishing breach spill over into a complex regulatory minefield. A successful attack puts your compliance with several critical frameworks at risk, which can lead to big fines and mandated fixes. The Office of the Australian Information Commissioner (OAIC) takes data protection very seriously under the Notifiable Data Breaches (NDB) scheme.
A breach caused by a vished employee can be seen as a failure to maintain adequate security controls, which can trigger non-compliance penalties. For leaders in finance and insurance, that risk is even higher under frameworks like APRA CPS 234, which demands strict information security controls. A vishing incident could be seen as a direct violation, attracting immediate regulatory attention.
This reflects the wider fraud landscape reported by the Australian Bureau of Statistics (ABS), where 3.2 million Australians—or 15% of those aged 15 and over—experienced personal fraud in 2024-25. While much of the AU$2.2 billion lost to card fraud was reimbursed, the sheer volume of scams, often starting with a phone call, highlights the need for strong defences. To better understand how these threats impact your organisation’s unique risk profile, you can learn more about how to conduct a comprehensive risk assessment.
On top of that, a vishing attack can damage your standing against globally recognised standards and government directives:
- ISO 27001: A failure to stop a social engineering attack calls into question the effectiveness of your whole Information Security Management System (ISMS), especially your controls around access management and security awareness.
- ASD’s Essential Eight: A compromised user account directly undermines several of the Essential Eight maturity levels, including controls for restricting admin privileges and enforcing multi-factor authentication.
When you weigh up the potential regulatory fines and the damage to hard-won certifications, the business case for investing in anti-vishing measures becomes clear. The risk of doing nothing is simply too high.
Building Your Multi-Layered Vishing Defence Strategy

Defending your organisation against vishing is not about finding a single magic bullet. It requires a robust, multi-layered strategy. First, one must acknowledge that technology alone will never be enough. While technical controls provide a crucial foundation, genuine resilience against social engineering comes from strengthening your human layer.
A successful defence integrates technical safeguards with continuous staff training and proactive monitoring. This creates a security posture where each layer reinforces the others, making it significantly harder for an attacker’s phone call to escalate into a breach. It is about shifting from a reactive footing to a proactive one.
Fortifying the Technical Layer
Your first line of defence should always focus on making attacks technically harder to execute. This means implementing controls that limit an attacker’s potential access and disrupt their methods before they even reach an employee.
Start with core security hygiene. Implementing strict Identity and Access Management (IAM) policies is non-negotiable. Enforcing the principle of least privilege ensures that even if an attacker compromises a user’s account, their access is severely restricted, limiting the potential damage.
On top of that, consider these foundational controls:
- Call Filtering and Analysis: Modern VoIP and unified communications platforms can help identify and block calls from known malicious numbers or suspicious international origins.
- Multi-Factor Authentication (MFA): Enforce MFA across all critical applications. This acts as a powerful backstop, preventing an attacker from using stolen credentials without that second verification factor.
To truly build a multi-layered vishing defence, it’s vital to incorporate robust cybersecurity measures.
Building the Human Firewall
While technology provides the guardrails, your people are the active defenders on the front line. The goal here is to transform employees from potential targets into a vigilant human firewall, capable of identifying and reporting vishing attempts with confidence. This is not achieved through a one-off training session, but through continuous reinforcement.
Without robust employee training—proven to cut susceptibility by over 40% in 90 days—organisations risk devastating breaches. As vishing evolves with AI deepfakes, Australian mid-market firms must prioritise continuous monitoring to stay audit-ready and resilient.
The objective of security training is not just awareness; it’s about building muscle memory. Realistic simulations create a safe environment for employees to fail, learn, and develop the instinct to question and verify unusual requests.
Your training programme should be practical and ongoing, incorporating:
- Realistic Vishing Simulations: Regularly test employees with controlled, simulated vishing calls that mimic real-world attacker scripts. Use these results to identify vulnerable departments and refine your training content.
- Clear Reporting Channels: Establish a simple, no-blame process for employees to report suspicious calls immediately. This empowers them to act as sensors for your security team.
Adding Continuous Oversight with Managed Services
Even with strong technical controls and a well-trained workforce, determined attackers can sometimes find a way through. This is where continuous monitoring and response capabilities become critical. You need the ability to spot the subtle behavioural anomalies that often signal a breach in progress.
This is where a Managed Detection and Response (MDR) service provides immense value. An MDR team acts as an extension of your own, providing 24/7 monitoring of your network, endpoints, and cloud environments. They use advanced tooling and human expertise to hunt for threats that automated systems might miss.
For instance, an MDR service can detect suspicious activity like a user account suddenly accessing sensitive files outside of normal business hours. This could be an early indicator that credentials stolen via vishing are being used. You can learn more about how this works by exploring our overview of the modern Security Operations Centre. This final layer of professional oversight ensures that when an attack does slip past your initial defences, it is detected and contained rapidly.
Even with the best defences in place, a well-crafted vishing attack can occasionally find its mark. When that happens, a fast, organised response is your best tool for limiting the damage. A clear playbook takes the panic and guesswork out of the equation, letting your team act with precision when the pressure is on.
The response must kick in the moment an employee even suspects they have been targeted. Every second counts. Those first few minutes can be the difference between a minor hiccup and a major breach, as attackers work quickly to gain a foothold or steal data.
Immediate Actions for Employees
The employee who took the call is your first line of defence. They need to know they can act immediately without fear of blame. Their job is simple: raise the alarm, fast.
- Disconnect Immediately: The employee must get their device off the network. That means pulling the ethernet cable and turning off Wi-Fi to cut the attacker’s connection.
- Report Through a Dedicated Channel: They need to report the incident to your security contact or IT helpdesk using a pre-agreed, out-of-band method, like calling from a personal mobile phone.
- Do Not Touch Anything: Instruct employees not to try and ‘fix’ the problem themselves. No logging off or shutting down unless specifically told to do so. This preserves critical evidence for the investigation.
As part of your planning, it is also worth knowing how to legally record suspicious phone calls for evidence, making sure you stay within Australian legal boundaries.
The Security Team Response Framework
Once the alarm is raised, the security team or your incident response provider steps in. They follow a structured framework to contain, eradicate, and recover from the attack, systematically taking back control.
In the face of a breach, a methodical response framework is non-negotiable. It transforms chaos into a controlled process, ensuring that every action taken is deliberate, effective, and serves to minimise business impact while preserving evidence for post-incident analysis.
The technical response moves through these phases:
- Containment: The first priority is to stop the bleeding. This means immediately locking any compromised user accounts, resetting all their passwords, and making sure the affected device stays completely isolated from the network to prevent the attacker from moving laterally.
- Eradication: Next, the team has to completely remove the attacker’s presence. This involves hunting down and removing any malware or remote access tools and triple-checking that no backdoors have been left behind. Often, this means wiping and reimaging the compromised machine from a known good state.
- Recovery: Once the threat is gone, you can safely restore operations. This involves restoring data from clean, verified backups, reissuing new credentials, and closely monitoring all systems for any lingering signs of malicious activity.
For sophisticated attacks, getting specialist support is essential. CyberPulse’s vCISO and managed detection services help you counter this threat by simulating vishing attacks during penetration testing and providing real-time incident response, ensuring you stay aligned with ISO 27001 and IRAP requirements.
Finally, a post-incident review is a must. You need to analyse exactly what happened, how the attacker got in, and where your existing controls fell short. This feedback loop is what strengthens your defences and refines your vishing incident response plan for the future, ensuring the organisation learns from the event and becomes more resilient.
Frequently Asked Questions About Vishing
We get a lot of questions about vishing from Australian business leaders. Here are a few of the most common ones, with straight-to-the-point answers to help lock in your understanding of this threat.
How Is AI Making Vishing More Dangerous?
AI-powered voice cloning, or ‘deepfakes’, has dramatically raised the stakes. Attackers can take just a small audio sample of a person’s voice—often scraped from social media or a company video—and use AI to create a scarily accurate clone.
Imagine a convincing call from your CEO, with their exact tone and speech patterns, pressuring an employee to make an urgent payment. This makes it almost impossible to spot a fake based on voice alone. It forces the need for strict procedural checks, like out-of-band verification, to become your primary defence, not just relying on recognition.
Are Mobile Phones As Vulnerable to Vishing?
Yes, absolutely. Mobile phones are a huge target for vishing attacks, partly because we are all so attached to them. Attackers often start with a text message (a technique called ‘smishing’) to create a sense of urgency before they even call.
The lines between our work and personal lives are blurred on our mobiles. A fraudulent call on a personal device can feel more intimate and pressing, making employees more likely to drop their guard and act on impulse rather than follow security protocols.
The single most effective defence against vishing is a well-trained and empowered workforce. While technology provides essential safeguards, human vigilance remains the ultimate control.
What Is the Most Effective Control Against Vishing?
Technical controls like call filtering and Multi-Factor Authentication are critical layers, but your strongest defence is always going to be your people. A solid ‘human firewall’ is by far the most effective control.
You build this through consistent, engaging security awareness training paired with regular, realistic vishing simulations. This creates a culture of healthy scepticism where employees feel confident enough to question and independently verify any unusual request, no matter how senior the person making it seems to be. Understanding what is vishing is the first step, but building this human resilience is what truly protects your organisation.
Fortify your organisation against sophisticated threats like vishing. CyberPulse provides expert-led security awareness training, realistic vishing simulations, and managed detection and response services to build a resilient, audit-ready defence. Secure your business and achieve continuous compliance by visiting us at https://www.cyberpulse.com.au.
Browse to Read Our Most Recent Articles & Blogs
Subscribe for Early Access to Our Latest Articles & Resources
Connect with us on Social Media

