Traditional penetration testing has a fundamental timing problem. A point-in-time engagement gives...
Managed SIEM Services: An AU CISO’s Guide for 2026

First Published:
Content Written For:
Small & Medium Businesses
Large Organisations & Infrastructure
Government
Read Similar Articles
Cloud Computing Security Services for Australian Businesses
As Australian businesses accelerate their move into the cloud, securing those digital environments...
SMB1001: A Cybersecurity Framework Guide for Australian Businesses
This article provides a guide to the SMB1001 framework. Cyber attacks now hit Australian...
How to defend against Infostealer Malware
Infostealer malware is not just another cyber threat. It is a silent data thief designed to...
A Guide to NIST Cybersecurity Framework Implementation
Getting a NIST Cybersecurity Framework implementation right is a strategic project, not just a...
Managed siem services are on the shortlist for many Australian security leaders for one simple reason. Internal teams are trying to cover enterprise log volumes, compliance evidence, and round-the-clock response with limited staff and uneven tooling. That model breaks under pressure, especially when the board expects stronger resilience, faster reporting, and cleaner audit outcomes at the same time.
Most CIOs and CISOs do not have a technology problem first. They have an operating model problem. Alerts arrive after hours, log sources are only partly onboarded, and no one wants to discover during an IRAP review or PCI-DSS assessment that retention, tuning, or response workflows were never production-ready. Managed SIEM is part of the CyberPulse Managed Detection and Response Service.
The Modern CISO’s Dilemma and the Role of Managed SIEM
Australian security leaders are carrying more risk with fewer practical options than many vendor brochures admit. The issue is not whether your SIEM can ingest logs. The issue is whether your team can tune detections, investigate alerts properly, and sustain 24×7 response capability without burning out the people you cannot easily replace.
That pressure is not hypothetical. Demand for managed siem services is rising in Australia alongside a significant increase in reported cybercrime, while Australian organisations using AI-enhanced SIEM automation saved an average of AUD $2.8 million per breach.
What breaks in an internal model
In practice, most internal SIEM programmes stall in three places:
- Detection engineering falls behind: New cloud workloads, identity changes, and SaaS integrations appear faster than teams can tune use cases.
- After-hours coverage is thin: An alert at 2 am is only useful if someone can triage it, validate it, and act.
- Compliance evidence stays manual: Audit artefacts often sit in spreadsheets, screenshots, and tribal knowledge.
A tool purchase does not solve any of that on its own.
Managed SIEM works when it is treated as a capability layer, not a log bucket. The provider takes responsibility for collection, correlation, tuning, and monitoring. Your team keeps ownership of risk decisions, internal escalation, and business context.
Why boards approve it
Boards rarely approve security spend for “better dashboards”. They approve spend when the service improves resilience, shortens detection cycles, and supports governance.
Practical test: If your current SIEM cannot support an incident at night, produce reliable audit evidence, and give the CISO a clear escalation path, it is not a mature control. It is a partially implemented platform.
The strongest business case for managed SIEM is straightforward. It augments scarce skills, closes operational gaps, and gives the organisation a service model that can be measured against risk, compliance, and response outcomes.
Managed SIEM vs MDR vs Co-Managed SOC
Many buying teams still compare the wrong services. That usually leads to a poor decision. They ask a managed SIEM provider to deliver hands-on containment, or they buy MDR expecting deep compliance reporting and long-term log retention.
Those are related services, but they are not interchangeable.
Managed Security Service Models Compared
| Criterion | Managed SIEM | Managed Detection and Response (MDR) | Co-Managed SOC |
|---|---|---|---|
| Primary function | Centralised log management, correlation, alerting, and compliance reporting | Human-led detection, investigation, and active response to threats | Shared operating model between provider and in-house team |
| Typical scope | Log source onboarding, use case tuning, dashboards, monitoring, reporting, retention | Endpoint, identity, cloud and network telemetry with analyst-led triage and containment | Joint workflows, shared queues, agreed responsibilities, custom escalation paths |
| Data sources | Broad log ingestion across infrastructure, cloud, applications, identity, and security tools | Typically prioritises high-value telemetry for rapid detection and response | Depends on the maturity of both parties and the selected tooling stack |
| Primary outcome | Better visibility, evidence, and monitoring discipline | Faster threat validation and response action | Better control for mature teams that still need external depth and after-hours support |
| Ideal use case | Organisations with compliance-heavy environments and fragmented visibility | Organisations needing rapid response and threat hunting with limited internal SOC capability | Organisations with an existing security team that wants to retain oversight but fill coverage gaps |
What each model is best at
Managed SIEM is best when the organisation needs order. It centralises evidence, enforces retention, and creates a structured detection layer across hybrid environments.
A managed Detection and Response Service is different. It focuses on identifying active threats, validating incidents quickly, and supporting or executing containment actions.
Co-managed SOC sits between the two. It works well for Australian organisations with a capable internal security or infrastructure team but no realistic way to cover every shift, every triage queue, and every investigation path.
Common buying mistakes
- Choosing SIEM when the primary gap is response: If your team cannot investigate and contain threats quickly, visibility alone will not reduce risk enough.
- Choosing MDR without evidence requirements in mind: If you need richer audit trails, broad ingestion, and policy-aligned retention, MDR on its own may not cover the governance need.
- Ignoring the operating model: A service fails when roles are vague. Someone must own triage, escalation authority, business communications, and remediation decisions.
The right answer for many Australian enterprises is not either-or. It is a defined mix of SIEM, response capability, and shared governance.
Key Capabilities of Effective Managed SIEM Services
A managed SIEM service earns its keep through operational detail. If the provider cannot explain who tunes rules, who validates alerts, and how evidence is retained, you are not buying a service. You are buying outsourced ingestion.

Monitoring that includes human judgement
Good providers do not just forward alerts. They run continuous monitoring with analysts who understand normal activity, suspicious behaviour, and the local business context.
That matters because poor tuning creates noise. Good tuning creates action. In Australian environments with hybrid infrastructure, identity systems, Microsoft security controls, and cloud workloads, rule logic needs regular review, not one-off implementation.
Retention and detection engineering
Effective managed siem services reduce mean time to detect by up to 70% compared with traditional SIEM, and they automate retention for 1 year or more, which directly supports Australian needs around ISO 27001 audit trails and IRAP assessments.
That headline matters less than what sits underneath it:
- Broad collection coverage: Identity, endpoint, firewall, cloud control plane, application, and admin activity logs need to arrive consistently.
- Normalisation and parsing: Data has to be usable, not just stored.
- Use case maintenance: Detections need updates as your environment changes.
- Retention discipline: Audit and investigation needs should be built into the service design.
Key takeaway: The value of managed SIEM is not log storage. It is reliable detection engineering plus evidence you can use.
What strong service delivery looks like
A capable provider should be able to show you:
- Onboarding methodology for critical log sources first.
- Escalation paths that define who gets called and when.
- Threat intelligence integration that is relevant to your environment.
- Reporting that supports decisions, not vanity metrics.
- Response support boundaries so there is no confusion during an incident.
What does not work is a generic package with little local tuning. If a service treats every tenant the same, your analysts will still drown in low-value alerts and your compliance team will still chase evidence manually.
Meeting Australian Compliance with Managed SIEM
Compliance is where many global managed SIEM offers fall short in Australia. They talk about generic frameworks, but local buyers need answers on ASD Essential Eight, IRAP, the Privacy Act 1988, APRA-aligned expectations, and evidence quality.
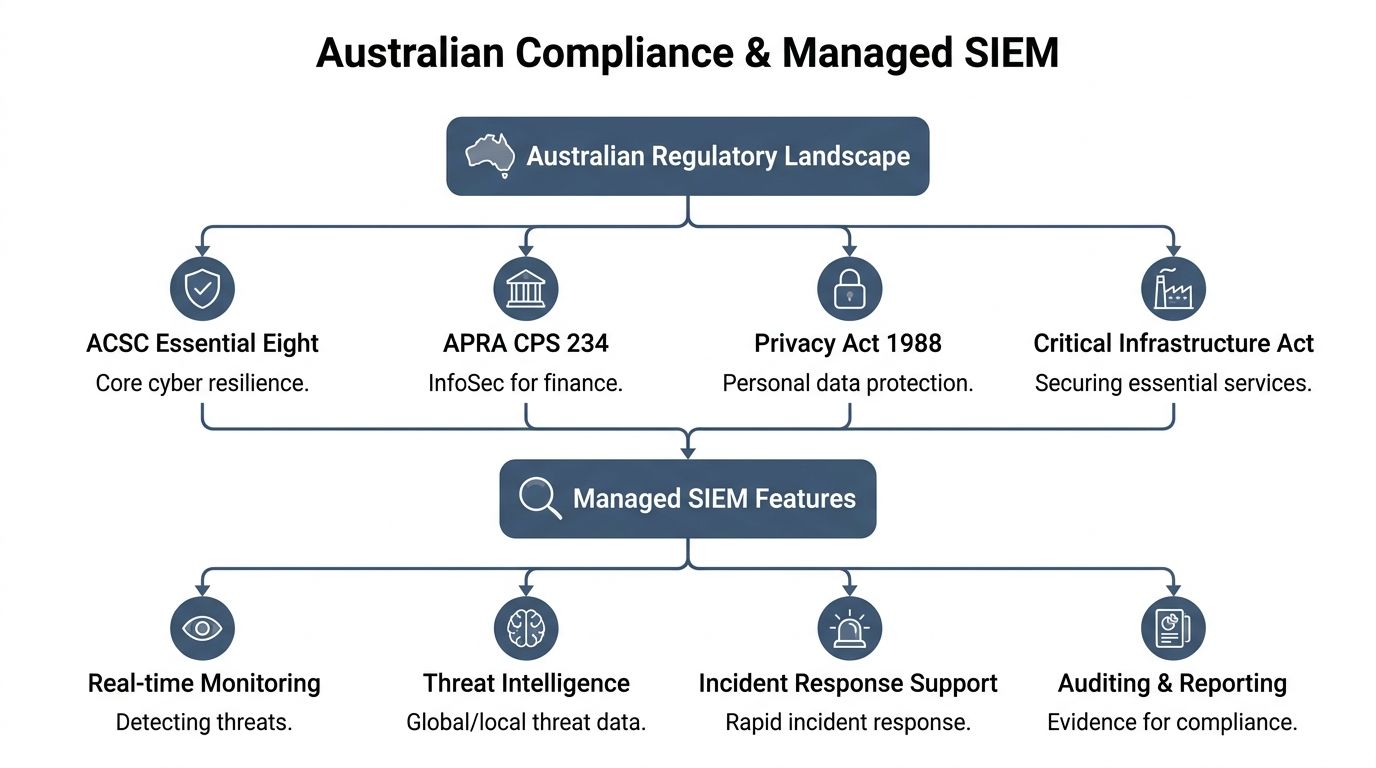
A provider can have a polished platform and still be the wrong fit if it cannot support sovereign data handling, local reporting needs, and control mapping that makes sense during audit.
Essential Eight and IRAP require more than alerts
A 2025 Deloitte AU cybersecurity survey found that only 22% of Australian mid-market firms using managed SIEM achieve full alignment with the ASD Essential 8, highlighting a tuning gap around local compliance and data sovereignty requirements under the Privacy Act 1988 and IRAP mandates.
That gap is familiar. Many services collect logs but do not map detections, retention, and reporting to the control intent behind Australian frameworks.
For example, managed SIEM can support:
- ASD Essential Eight: Monitoring privileged activity, suspicious execution patterns, and control failures gives security teams better evidence of how controls operate in practice.
- IRAP readiness: Consistent collection, retention, and query capability help organisations demonstrate audit trails and event visibility.
- Privacy Act obligations: Local hosting and clear handling of personal information reduce uncertainty around where sensitive telemetry resides.
Compliance evidence must be operational
The best providers treat compliance as an operational by-product of security monitoring. They do not create a separate, manual reporting layer at the end of the month.
That means the service should generate:
- Consistent logs from agreed systems
- Searchable records for investigations and audits
- Standard reports for risk, control owners, and auditors
- Clear records of escalations and response actions
This is especially relevant for financial services and other regulated sectors that must align security operations with governance. Teams evaluating provider fit should also consider how the monitoring service supports broader obligations such as APRA CPS 234 compliance in Australia.
Data sovereignty is not a footnote
Australian CISOs should ask direct questions about where telemetry is stored, who administers the platform, and how access is controlled. If the answer is vague, the risk is real.
Practical advice: Ask the provider to walk through one audit scenario and one incident scenario. If they cannot show how logs, access records, and analyst actions would be produced for both, their compliance story is probably too thin.
A managed SIEM service helps compliance when it is designed around evidence quality, local control expectations, and repeatable operating procedures. Without that, it becomes another platform that auditors do not trust.
Your Vendor Selection Checklist
Vendor selection is where commercial discipline matters. A lower monthly fee often hides shallow onboarding, generic content packs, and offshore escalation that does not fit your regulatory posture.
Australian buyers should score providers on service depth, not on slide quality.

Non-negotiables for a serious shortlist
For Australian enterprises needing PCI-DSS or SOC 2 compliance, top-tier providers can deliver sub-15-minute MTTR by integrating SOAR and AU-centric threat intelligence. That matters because untuned SIEMs can generate over 10,000 daily alerts, which overwhelms internal teams, according to SentinelOne’s overview of managed SIEM services.
Use that as a threshold question. Then go deeper.
- Local operating context: Ask whether the provider has genuine Australian delivery capability, including people who understand local regulatory expectations and business hours support requirements.
- Platform clarity: Confirm whether the service runs on Microsoft Sentinel, another SIEM platform, or a mixed stack. You need to know what is native, what is custom, and what is extra cost.
- Tuning ownership: Ask who writes and maintains detection logic after onboarding.
- Response boundaries: Clarify whether the provider only notifies, or whether they support containment workflows and orchestration.
- Evidence quality: Review sample reports for board use, operational use, and audit use. They should not all look the same.
Commercial checks that prevent regret
A good procurement process for managed SIEM should cover more than scope and price. It should validate assumptions around support hours, onboarding effort, retention, and change management. Disciplined information technology procurement makes a material difference.
Ask questions such as:
| Checkpoint | What to verify |
|---|---|
| Onboarding scope | Which log sources are included in the base service and which are charged separately |
| Service levels | Detection, triage, escalation, and reporting commitments |
| Data handling | Storage location, access model, retention settings, and export options |
| Change process | How new systems, business units, and detection requirements are added |
| Exit readiness | How logs, detections, and reporting artefacts can be handed back if the contract ends |
Buyer’s rule: If a provider cannot explain the service in operational terms, assume the actual workload will fall back on your internal team.
The strongest vendors are transparent about trade-offs. They will tell you what they automate, what still needs customer input, and where a co-managed model may be better than a fully outsourced one.
Implementation Steps and Measuring True ROI
A managed SIEM deployment should be run like a control uplift programme, not a software rollout. That changes the sequence and the success measures.
What implementation usually looks like
Most successful rollouts follow a practical order:
-
Discovery and scoping
Identify crown-jewel systems, compliance drivers, and the log sources that matter first. -
Onboarding and parsing
Connect the highest-value telemetry before chasing long-tail sources. -
Use case tuning
Build and refine detections around realistic threat scenarios and control failures. -
Escalation design
Define who receives alerts, who approves action, and how incidents move after hours. -
Go-live with review cycles
Expect tuning adjustments after production traffic starts flowing.
What does not work is onboarding everything at once. That usually creates a backlog of parsing issues, poor-quality detections, and immediate frustration from internal teams.
Measuring ROI in terms the board accepts
Australian SMEs struggle with in-house SIEM costs averaging AUD $250,000 annually due to skills shortages, while fixed-cost managed SIEM can yield 30-40% savings, according to KBV Research’s managed SIEM market summary.
That cost argument is useful, but mature buyers should measure more than budget reduction.
Track value across four areas:
- Operational efficiency: Fewer internal hours spent on routine monitoring and evidence gathering.
- Detection and response quality: Whether incidents are identified and escalated faster in practice.
- Audit readiness: Whether compliance teams can obtain usable artefacts without manual reconstruction.
- Staff focus: Whether internal engineers can focus on hardening, architecture, and remediation rather than queue management.
Some organisations also use an analyst-assessed ROI model to evaluate service value over time. If you want a structured benchmark for that approach, the ROI of managed detection and response resource is a useful reference point for framing board-level discussions.
Metrics that matter more than dashboard volume
Do not let the provider report success based on raw event counts or the number of alerts processed. Those are activity metrics.
Use outcome metrics instead. Focus on whether the service reduces investigative drag, supports cleaner decision-making, and improves resilience during real incidents.
Beyond Alerts to True Cyber Resilience
The strongest case for managed siem services is not convenience. It is control. Australian organisations need a security operating model that handles real alert volume, supports local compliance duties, and gives leaders confidence that incidents will not sit unattended outside business hours.
A well-run service gives the CISO three things that matter. Better visibility. Better evidence. Better response discipline.
That still leaves one important decision. You need the right blend of monitoring, detection engineering, and threat response for your risk profile. For many organisations, that means combining SIEM capability with stronger response workflows and ongoing intelligence-led tuning. Teams that want to strengthen that broader model should also review how cyber security threat intelligence feeds detection quality and prioritisation.
The practical test is simple. If the service helps your team make faster, better decisions under pressure, it is building resilience. If it just stores more logs, it is not.
CyberPulse helps Australian organisations turn monitoring into measurable security outcomes. If you need commercially grounded advice on managed SIEM, MDR, IRAP, Essential Eight, PCI-DSS or audit-ready security operations, speak with CyberPulse.
Browse to Read Our Most Recent Articles & Blogs
Subscribe for Early Access to Our Latest Articles & Resources
Connect with us on Social Media

