This article provides a guide to the SMB1001 framework. Cyber attacks now hit Australian...
Risk Management in Supply Chains for Australian Businesses: CIO Guide

First Published:
Content Written For:
Small & Medium Businesses
Large Organisations & Infrastructure
Government
Read Similar Articles
How to defend against Infostealer Malware
Infostealer malware is not just another cyber threat. It is a silent data thief designed to...
A Guide to NIST Cybersecurity Framework Implementation
Getting a NIST Cybersecurity Framework implementation right is a strategic project, not just a...
What Is an Intrusion Test? A Guide for Australian Businesses
An intrusion test is an authorised, simulated attack on your organisation's systems, networks, or...
What is Endpoint Detection and Response?
Think of Endpoint Detection and Response (EDR) as an elite security detail for every single device...
Effective risk management in supply chains is no longer just an operational task. Instead, it is a critical boardroom conversation, essential for business continuity, data protection, and regulatory compliance in an unpredictable global economy.
Done well, it means you identify, assess, and mitigate potential disruptions across your entire network of suppliers. This guide provides a commercially grounded framework for Australian technology leaders to master this challenge.
The New Reality of Australian Supply Chain Vulnerabilities

For Australian CIOs and CISOs, abstract supply chain risks have become very real, persistent threats. In fact, the same interconnectedness that drove efficiency now creates cascading points of failure. A single weak link—a logistics partner, a SaaS provider, or a component manufacturer—can introduce huge operational and cyber risks.
These are not isolated incidents anymore. For instance, a factory shutdown on the other side of the world can halt production in Melbourne. Similarly, a data breach at a third-party vendor can expose sensitive Australian customer data, triggering regulatory fines and reputational carnage.
The challenge for leaders is that these risks are converging; a physical disruption is often tangled up with a digital one. You can read more about the current landscape in the latest ASD Cyber Threat Report for Australia.
From Global Shocks to Local Impacts
Global geopolitical and economic events now hit local operations directly and quickly. Consequently, we’ve seen a clear resurgence of supply chain disruptions in Australia, much of it triggered by external trade policies.
Recent research highlights this, showing that by August 2026, 47% of Australian industries reported active supply chain disruptions—a 12% increase in just nine months. At the same time, 45% of industrial firms pointed to domestic regulations as a major barrier to investing in more resilience. This shows a complex tension between external pressures and internal constraints.
This new reality, therefore, demands a fundamental shift in thinking. Reactive, siloed approaches just do not cut it anymore.
Why a Proactive Security Mindset Is Non-Negotiable
A proactive, security-first approach to risk management in supply chains is now a basic requirement for business survival. Waiting for a disruption to happen is a strategy destined to fail. Instead, organisations must get ahead of vulnerabilities across their entire supplier ecosystem.
This means baking security into every stage of procurement and partnership. Furthermore, it means asking tough questions before you onboard a new vendor:
- What does their security posture look like?
- How will they protect our data?
- What are their incident response capabilities?
For Australian leaders, the goal is clear: build resilience by design, not by default. This means moving beyond compliance checklists to foster a culture where every partner is treated as an extension of your own security perimeter.
Ultimately, robust supply chain risk management protects revenue, safeguards your brand, and ensures you can deliver for your customers, even when the unexpected happens.
Building Your Risk Taxonomy and Governance Framework
A structured defence against supply chain risk starts with defining exactly what you’re trying to protect. For Australian leaders, this means moving beyond vague concerns and creating a precise, catalogued system. You need a risk taxonomy a classification scheme that categorises all potential threats to your supply chain.
Without this clarity, teams operate in silos, reacting to problems instead of pre-empting them. Therefore, a solid taxonomy ensures everyone from procurement to the C-suite speaks the same language about risk. It is the foundation of any strong governance model.
Defining Your Supply Chain Risk Categories
To build a useful taxonomy, you need to look beyond simple operational hiccups. Modern supply chains face a complex web of interconnected risks. Your framework, therefore, has to break down these threats into distinct, manageable categories.
A good starting point is to classify risks across four key domains:
- Operational Risks: These are the threats to the day-to-day execution of your supply chain. Think supplier production failures, quality control issues, logistics bottlenecks, or inventory shortages. A key component supplier in Southeast Asia facing a factory shutdown due to local flooding is a classic operational risk.
- Financial Risks: This category covers any financial instability within your supply chain. For example, this could be a critical vendor on the brink of bankruptcy, unpredictable price volatility for essential raw materials, or currency fluctuations that destroy your margins.
- Compliance and Reputational Risks: This involves a supplier failing to meet legal, regulatory, or ethical standards. It could be a data breach that violates Australian privacy laws, a partner failing to meet modern slavery reporting requirements, or a supplier engaging in unethical labour practices that damage your brand.
- Cybersecurity Risks: This is a rapidly expanding category. It includes everything from a ransomware attack on a third-party software provider to data exfiltration through a compromised partner’s network access. Indeed, a successful phishing attack on a supplier’s employee could easily give attackers a foothold into your own systems.
This kind of categorisation turns an overwhelming problem into a set of specific challenges you can systematically address. It also helps align your supply chain efforts with broader governance, risk, and compliance (GRC) objectives. You can read more in our detailed guide on integrating your cybersecurity GRC framework to see how these pieces fit together.
Sample Supply Chain Risk Taxonomy Framework
To help organisations build a comprehensive risk register, we developed a sample framework that categorises key supply chain risks. Specifically, this table shows how different risk types, example scenarios, and relevant controls come together.
| Risk Category | Risk Type | Example Scenario (Australian Context) | Relevant Framework/Control |
|---|---|---|---|
| Operational | Production Disruption | A key agricultural supplier in Queensland is unable to fulfil orders due to severe drought conditions, impacting food production schedules. | Business Continuity Planning (BCP), Supplier Diversification |
| Financial | Supplier Insolvency | A critical logistics partner based in Melbourne enters voluntary administration, freezing your distribution network and delaying customer deliveries. | Financial Health Monitoring, Contractual Step-in Rights |
| Compliance & Reputational | Modern Slavery | A textile supplier in your tier-two supply chain is found to be non-compliant with Australia’s Modern Slavery Act reporting requirements. | Supplier Code of Conduct, Regular Audits, ISO 26000 |
| Cybersecurity | Third-Party Data Breach | A SaaS provider hosting your customer data suffers a ransomware attack, exposing personal information and triggering notifiable data breach obligations under Australian law. | ISO 27001 (A.15), Contractual Security Clauses, SOC 2 Report |
| Geopolitical | Trade Restrictions | The Australian government imposes sudden export controls on a raw material essential to your product, sourced from a specific country. | Geopolitical Risk Monitoring, Strategic Stockpiling |
Using a structured table like this helps ensure no major risk domains are overlooked. In addition, it provides a clear, auditable trail for risk management activities.
Establishing a Clear Governance Framework
Once you’ve defined your risks, you need a governance framework to manage them. This framework assigns ownership and defines the processes for making risk-based decisions. It is not a theoretical document; it’s a practical guide that embeds risk management into your organisation’s DNA.
A governance framework without clear accountability is just a document on a shelf. True governance ensures every individual, from the board down to the procurement team, understands their specific role in protecting the organisation from third-party risk.
Regulatory pressures also amplify these challenges for Australian businesses. For instance, Aon’s 2026 Global Risk Management Survey highlights how organisations are grappling with technology-led risks. Meanwhile, with 54% of Australian businesses reportedly lagging on ESG standards, scrutiny on supplier practices is only increasing, compounding the regulatory exposure from vendor-related cyber incidents. You can read the full research on these global risk trends to get a better sense of this shifting landscape.
Aligning with Australian and Global Standards
Your governance framework should not exist in a vacuum. For it to be effective and defensible, it must align with recognised standards that provide a proven structure for managing security and operational resilience. For Australian organisations, that means integrating key controls from both local and international frameworks.
Here are the key frameworks to consider:
- ISO 27001: As the global standard for Information Security Management Systems (ISMS), it provides a superb foundation. Its Annex A controls on supplier relationships (A.15) offer a clear roadmap for managing third-party information security.
- ASD’s Essential Eight: While focused on internal cyber hygiene, applying the principles of the Essential Eight to your suppliers is a powerful move. You should contractually require critical suppliers to demonstrate maturity against these controls, particularly those related to patching, access control, and application hardening.
- NIST Cybersecurity Framework (CSF): The NIST CSF’s five functions—Identify, Protect, Detect, Respond, Recover—provide an excellent lifecycle approach for your supply chain risk program. Applying this model helps ensure you cover all bases, from initial vendor assessment to joint incident response planning.
By building your taxonomy and governance around these established standards, you create a defensible, audit-ready program. This not only strengthens your security posture but also demonstrates due diligence to regulators, partners, and customers, solidifying trust in your operations.
Mastering Vendor Risk Assessment and Segmentation

Treating every supplier as an equal risk is a recipe for failure. Indeed, a one-size-fits-all approach to vendor management wastes time and money on low-impact partners while leaving your organisation dangerously exposed to the high-risk ones that truly matter.
Effective supply chain risk management depends on a disciplined approach to assessment and segmentation. It means you strategically sort vendors based on how critical they are to your operations and what level of access they have to your sensitive data.
Without this focus, your security and procurement teams will inevitably be overwhelmed. You’ll end up spending as much time vetting the office stationery provider as you do the cloud platform hosting your customer data, which is both inefficient and dangerous.
Moving Beyond Basic Questionnaires
The old-school approach of sending out a generic security questionnaire just doesn’t cut it anymore. While they can be useful for an initial screening, they often give you aspirational answers, not the ground-truth security posture of your vendor.
A supplier can easily tick a box claiming they perform regular patching, but this provides no real assurance. To truly understand a vendor’s risk profile, you must move from “what they say” to “what they do” by verifying their security claims with objective evidence.
Key areas for a deeper dive include:
- Security Certifications: Ask for proof of current certifications like ISO 27001 or a SOC 2 Type II report. These independent audits offer a far more reliable view of a vendor’s controls than a self-assessment ever could.
- Incident Response Capabilities: Do not just ask if they have a plan. Instead, ask for a redacted version or specific details on how they test it, their RTO/RPO targets, and their communication protocol in a crisis.
- Fourth-Party Risk: Dig into how they manage their own critical suppliers. A breach in their supply chain can very quickly become a breach in yours.
A Practical Vendor Tiering Strategy
The cornerstone of efficient vendor risk management is segmentation, or tiering. By grouping vendors into tiers based on their risk profile, you can focus your due diligence and monitoring resources where they have the most impact.
A simple yet powerful tiering model might look like this:
- Tier 1 (Critical): These are your most vital partners. For example, they might have deep access to sensitive data (like financial or health records), be tightly integrated into your network, or their failure would cause immediate and severe disruption to your business. Think of your primary cloud provider or a core payment gateway.
- Tier 2 (Important): These vendors are important to your operations but not as business-critical as Tier 1. They might handle less sensitive data or provide services that have workable, albeit inconvenient, alternatives. This could include a marketing automation platform or a specialised software provider.
- Tier 3 (Low Risk): This category is for vendors with minimal access to your systems or data. Their failure would have a negligible impact on your core business. Examples include an office cleaning service or your landscaping company.
The core principle is simple: match the intensity of your scrutiny to the level of risk. Tier 1 vendors demand continuous monitoring and deep-dive assessments, whereas Tier 3 vendors may only need a light-touch initial review.
An Initial Assessment Checklist
To standardise this process, an initial assessment checklist helps you quickly categorise new vendors. This ensures you consistently apply your risk criteria from the moment a new supplier relationship is on the table, and it should be a prerequisite for procurement.
Before you onboard any new vendor, ask these foundational questions:
- Data Access: Will the vendor access, process, or store sensitive company or customer data? This includes personal identifiable information (PII), financial records, or intellectual property.
- System Integration: Will the vendor’s systems connect directly to your internal network or production environments?
- Operational Criticality: If this vendor went down for 24 hours, what would be the impact on our business? Would it bring core operations to a halt?
- Regulatory Scope: Does this vendor’s service fall under specific compliance mandates for our industry, such as APRA regulations or the Privacy Act?
Answering “yes” to the first two questions almost automatically places a vendor in a higher risk tier. This structured approach removes guesswork and creates a defensible, auditable process for risk management in supply chains.
For a deeper exploration of this process, consider reviewing our strategic framework for vendor risk management for more detailed guidance. By focusing your expert resources where they matter most, you build a more resilient and secure extended enterprise.
Implementing Contractual and Technical Controls
Once you’ve identified, assessed, and segmented your supplier risks, it’s time to put your defences in place. This is where your strategy becomes action. Your controls fall into two key areas: the legal safeguards you write into contracts and the technical measures you deploy to watch over your digital connections.
For Australian organisations, these controls aren’t just good practice; they’re essential for compliance and survival. Simply trusting a supplier’s security promises is no longer a defensible position. You need to embed your security requirements directly into your legal agreements and actively prove they’re working with technical tools.
Forging Ironclad Supplier Contracts
Your supplier contracts are much more than commercial paperwork—they are fundamental security documents. In fact, they are your best tool for setting crystal-clear expectations and giving you legal options if a partner doesn’t hold up their end of the bargain. Vague phrases like “reasonable security” just will not cut it anymore.
Instead, your contracts must be precise, enforceable, and aligned with Australian regulatory expectations. This is a non-negotiable part of effective risk management in supply chains.
Here are the contractual clauses we see make the biggest difference:
- Right-to-Audit: This clause gives you the explicit power to assess a supplier’s security controls. It can cover anything from reviewing their documentation to performing onsite inspections or penetration tests, giving you a way to verify their security posture for yourself.
- Security Standards Alignment: Require compliance with specific frameworks. For your most critical suppliers, this should mean mandating standards like ISO 27001 or demonstrable maturity against the ASD Essential Eight.
- Data Breach Notification Timelines: Define strict, unambiguous deadlines for breach notification. Do not settle for wishy-washy terms like “in a timely manner.” Your contract should specify that they must notify you within a set period, like 24 or 48 hours, of finding an incident that affects your data or services.
- Liability and Indemnification: Clearly spell out who pays for what if a supplier-caused security incident occurs. This clause needs to cover costs for forensic investigations, regulatory fines, and customer notifications.
A well-crafted contract shifts the security conversation from a matter of trust to one of accountability. It ensures your security requirements are not just requests but binding obligations, protecting your organisation when things go wrong.
The need for strong contractual oversight is driven home by the rising tide of supply chain attacks. Cybersecurity supply chain risks have exploded, with the Australian Signals Directorate (ASD) responding to over 100 such incidents in the last financial year alone. The 2025 DP World Australia cyberattack, which brought major ports to a standstill, is a harsh reminder of the domino effect. In response, the Critical Infrastructure Annual Risk Review 2026 urges organisations to adopt an ‘all-hazards’ approach, which includes doing thorough due diligence on their suppliers’ cybersecurity. You can discover more insights in the full government review.
Deploying Proactive Technical Controls
While contracts set the rules of the game, technical controls are how you enforce them and spot when someone isn’t playing by them. These tools give you much-needed visibility into the digital connections you share with third parties. Consequently, they help you move from a passive, trust-based model to active, evidence-based assurance.
Think of effective technical controls as an early warning system. They help you spot strange behaviour before it snowballs into a full-blown crisis, acting as your eyes and ears across your entire extended digital ecosystem.
Key Technical Controls for Supplier Monitoring
Putting the right technical measures in place gives you confidence that your partners are actually meeting the security standards you’ve agreed to.
Here are some of the most effective controls for keeping tabs on third-party risk:
- Managed Detection and Response (MDR): An MDR service is vital for monitoring network traffic and endpoint activity across connections to third parties. By analysing telemetry from these connections, MDR teams can spot suspicious behaviour—like unusual data transfers to a supplier’s network—that might signal a compromise.
- Continuous Security Posture Monitoring: Automated tools can constantly scan your suppliers’ external-facing systems for vulnerabilities, misconfigurations, and outdated software. This gives you an objective, real-time snapshot of their security hygiene without having to rely on their own self-assessments.
- Automated Penetration Testing: For high-risk vendors, especially those with direct API integrations, an automated penetration testing platform is a smart move. These tools simulate attacks against the vendor’s application interfaces to find weaknesses proactively, before real attackers do.
Integrating these controls makes your entire approach to information technology procurement more robust. You can dive deeper into this topic in our guide on strengthening security in IT procurement. By combining strong legal agreements with proactive technical validation, you build a multi-layered defence that dramatically reduces your exposure to third-party risk.
Driving Continuous Assurance and Incident Response Readiness
A one-off vendor audit is a snapshot in time. It’s useful, but it tells you nothing about what’s happening today. The reality is that your vendors’ security postures are constantly changing, and effective risk management in supply chains must reflect that.
Simply assessing a supplier during onboarding and then filing the report away creates a dangerous false sense of security. To build genuine resilience, Australian organisations need to move away from periodic checks and embrace a model of continuous assurance. This means actively monitoring the security health of your supply chain and having a rock-solid plan for when—not if—one of your partners has an incident.
Establishing KPIs for Continuous Monitoring
Without clear metrics, supply chain risk management becomes a guessing game. Key Performance Indicators (KPIs) are essential for turning a subjective process into a measurable business function. Furthermore, they give you an early warning system for emerging problems.
Your KPIs should move beyond simple compliance checklists. Instead, focus on metrics that give you a real-world view of your risk exposure.
- Vendor Compliance Drift: Track the percentage of critical vendors who fall out of line with your contractual security requirements. A rising number here points to a systemic breakdown in your program.
- Time to Remediate: Measure the average time it takes a vendor to fix a critical vulnerability after you’ve flagged it. Long remediation times are a massive red flag, often indicating a poor security culture.
- Third-Party Incidents: Count the number of security incidents originating from your supply chain partners each quarter. This is the ultimate measure of your program’s real-world effectiveness.
These data points allow you to have fact-based conversations with vendors, justify security investments, and focus your team’s limited time on the partners who genuinely pose the greatest risk.
Developing and Testing Incident Response Playbooks
When a supplier gets breached, it’s your problem too. However, a generic incident response plan won’t cut it. You need specific, tested playbooks designed for third-party incidents because the entire response process is different when you don’t own the compromised systems. A critical part of this is actively managing supply chain disruptions before they escalate.
A third-party incident response playbook is your organisation’s emergency procedure for a crisis you can’t directly control. Without a pre-defined and rehearsed plan, you will be scrambling to make critical decisions under extreme pressure, wasting precious time while the damage spreads.
Your playbooks need to be tailored to different scenarios. A ransomware attack locking up a key logistics partner, for example, requires a completely different response than a data breach at a marketing SaaS provider. If you’re building out your foundational plan, our detailed guide on developing a computer incident response plan is a great place to start.
The process of managing supply chain controls is a continuous loop, moving from initial assessment to contracting and then into ongoing monitoring, which then feeds back into the assessment phase.
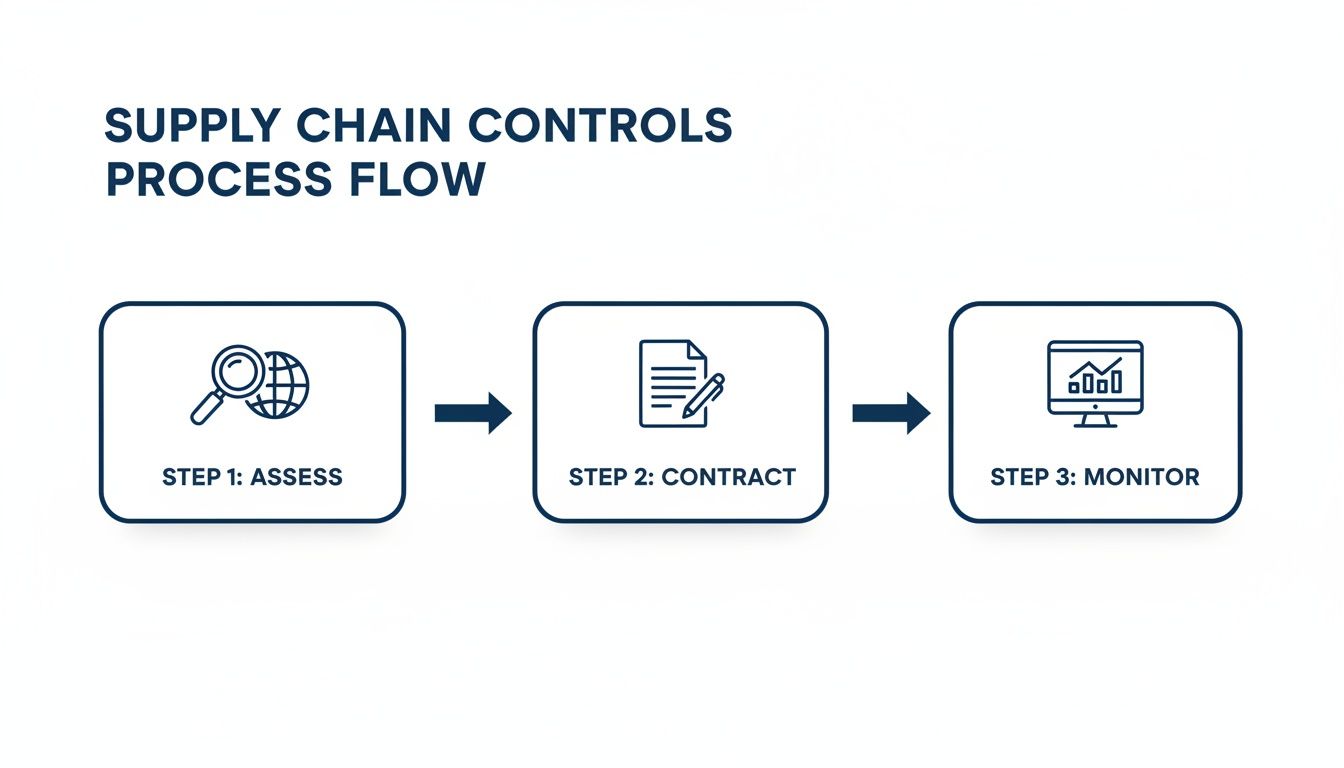
This cycle makes it clear that risk management isn’t a project with an end date. It’s an operational rhythm where what you learn from monitoring directly informs your next assessment.
A Scenario: An Australian SaaS Provider Breach
Let’s walk through a realistic scenario. Your organisation depends on an Australian SaaS provider for its CRM system. On a Monday morning, your CISO gets a call from the provider’s CEO: they’ve been breached. An attacker has accessed customer data, including data belonging to your clients.
Because you have a tested incident response playbook, your team moves with purpose, not panic.
Mobilise the Core Team
The first action is to bring together the pre-designated incident response team. This is not a random collection of people; it’s a specific group including legal, communications, IT security, and the business relationship owner for the breached vendor. Everyone already knows their role.
Activate Fact-Finding Protocols
Your technical team immediately engages with the vendor to get the facts. They are not just waiting for information; they are actively asking the hard questions:
- What specific data relating to our customers was accessed or stolen?
- What is the exact timeline of the breach?
- What containment and eradication steps have you taken right now?
- What was the root cause of the compromise?
Enact Containment Measures
While the vendor works on their internal mess, your team takes immediate steps to protect your own environment. This means rotating any API keys or credentials shared with the vendor and hunting through network logs for any sign of lateral movement from their systems into yours.
Manage Stakeholder Communications
Your legal and communications teams get to work, drafting initial holding statements based on confirmed facts, not speculation. They assess whether you have an obligation to report the incident under Australia’s Notifiable Data Breaches (NDB) scheme. A plan for clear, transparent communication with your own affected customers is set in motion.
Post-Incident Review
Once the immediate fire is out, a thorough post-mortem is scheduled. The goal here is not to assign blame but to learn. The review will measure the vendor’s response against their contractual security obligations and help you decide whether the relationship needs to be re-evaluated or even terminated.
This structured response turns a potential disaster into a managed event. It allows your organisation to meet its legal duties and, most importantly, maintain the trust of your customers.
Aligning with Australian Compliance Frameworks
While managing third-party risk is a practical security issue, it’s also a core part of compliance. In Australia, several key frameworks provide structure for building a robust supply chain security program. Understanding how they fit together helps you build a program that is both effective and defensible to auditors and regulators.
Australian Compliance Frameworks for Supply Chain Security
| Framework | Primary Focus | Key Supply Chain Relevance | Best For |
|---|---|---|---|
| ISO 27001 | Information Security Management Systems (ISMS) | Clause 15 (Supplier Relationships) requires formal processes for managing risks associated with suppliers and third parties. | Organisations needing a globally recognised, structured framework for overall security governance. |
| NIST CSF | Cybersecurity Risk Management | The “Identify” function includes specific subcategories for supply chain risk management (ID.SC), providing a detailed roadmap. | Organisations seeking a flexible, risk-based framework that is highly respected in both government and enterprise sectors. |
| ASD Essential 8 | Foundational Mitigation Strategies | While not a full supply chain framework, its controls (e.g., patching, access control) are foundational requirements you must flow down to critical vendors. | Establishing a non-negotiable baseline of technical security hygiene for both your own environment and your key suppliers. |
| SOC 2 | Service Organisation Controls | For SaaS and managed service providers, a SOC 2 report provides assurance over the security, availability, and confidentiality of their services. | Evaluating the control environment of your software and service providers, especially those handling sensitive data. |
While each framework has a different emphasis, they all point to the same conclusion: you are responsible for the security of your data, no matter where it lives. Integrating these standards into your vendor risk program provides a clear, auditable structure for meeting that responsibility.
Frequently Asked Questions About Supply Chain Risk Management
When it comes to making supply chain security a reality, Australian business leaders often ask us some very pointed questions. We've compiled the most common ones we hear, along with our direct, commercially grounded advice to help you strengthen your organisation’s defences.
How Can We Quantify Vendor Risk in a Meaningful Way?
Quantifying vendor risk is about moving it from a gut feeling to a data-driven decision. The most practical way to start is with a risk scoring matrix that combines impact and likelihood.
First, think about the real-world business impact if a vendor went down. This is not just about the financial hit; consider reputational damage, regulatory fines under the Privacy Act, and operational chaos. You should assign a score, say from 1 (low impact) to 5 (catastrophic).
Next, assess the likelihood of an incident based on objective proof. A vendor with a current SOC 2 Type II report and a mature security program is a much safer bet than one with no certifications and a visibly poor security posture. Again, score this from 1 (very unlikely) to 5 (very likely).
Multiply these two scores (Impact x Likelihood) to get a final risk rating for each vendor. This simple calculation gives you a clear, defensible method for prioritising which suppliers need the most intensive oversight.
This quantitative approach helps focus your effort where it matters. Furthermore, it gives you a clear justification for your risk management in supply chains strategy when you talk to the board.
What’s the Best Way to Handle a Critical Supplier Who Is Not Meeting Our Security Requirements?
This is a delicate but all-too-common situation. You cannot just offboard a critical, non-compliant supplier without causing massive disruption. The approach has to be collaborative but firm, escalating through clear, pre-defined stages.
-
Formal Notification: Start by formally documenting the specific security gaps in writing. Be sure to reference the contractual clauses they are breaching and provide a reasonable, non-negotiable timeline for them to present a remediation plan.
-
Collaborative Planning: Your goal is to help them improve, not just to penalise them. Therefore, work with the supplier to develop a corrective action plan (CAP) that includes clear milestones, owners, and check-in dates.
-
Increased Monitoring: While they work on the plan, you need to increase your own vigilance. This could mean more frequent vulnerability scans or heightened scrutiny of network traffic flowing between your organisations.
-
Executive Escalation: If you see progress stalling, do not wait. You should escalate the issue to the executive sponsors on both sides. This ensures senior leaders are aware of the business risk and can apply the commercial pressure needed to get things moving.
If, after all that, the supplier remains unable or unwilling to meet your requirements, you have to be ready to activate your contingency plan. This means transitioning to an alternative, pre-vetted supplier. It might cause short-term pain, but accepting indefinite risk from a critical partner is never a sustainable strategy.
Can We Automate Third-Party Risk Management?
Yes, and to be honest, you absolutely have to. Manually tracking the security posture of dozens, let alone hundreds, of suppliers is simply impossible to do effectively at scale. Automation is what makes an efficient and effective program possible.
Several tools can automate different parts of the process:
- Security Rating Platforms: These services give you a continuous, outside-in view of your vendors' external attack surfaces, providing a dynamic score based on factors like patching cadence, open ports, and dodgy configurations.
- Questionnaire Automation: Instead of juggling spreadsheets, these platforms can streamline the sending, collection, and analysis of security questionnaires, automatically flagging high-risk answers for your team to review.
- Threat Intelligence Feeds: Integrating threat intelligence means you get automated alerts if a vendor appears in data breach dumps or is being discussed in dark web chatter.
However, automation is not a silver bullet. It’s brilliant at collecting data and flagging potential issues, but you still need a security professional to interpret the results, understand the context, and make the final risk-based decision. The goal is to use automation for the 80% of routine work, freeing up your experts to focus on the 20% of high-impact analysis and strategic engagement.
At CyberPulse, we help Australian organisations move from reactive, point-in-time checks to a model of continuous assurance. If your current vendor risk program feels more reactive than strategic, we can help you build a resilient, audit-ready framework. Learn how our tailored GRC and vendor risk management solutions can protect your business at https://www.cyberpulse.com.au.
Browse to Read Our Most Recent Articles & Blogs
Subscribe for Early Access to Our Latest Articles & Resources
Connect with us on Social Media

