This article provides a guide to the SMB1001 framework. Cyber attacks now hit Australian...
Cloud Computing Security Services for Australian Businesses

First Published:
Content Written For:
Small & Medium Businesses
Large Organisations & Infrastructure
Government
Read Similar Articles
How to defend against Infostealer Malware
Infostealer malware is not just another cyber threat. It is a silent data thief designed to...
A Guide to NIST Cybersecurity Framework Implementation
Getting a NIST Cybersecurity Framework implementation right is a strategic project, not just a...
What Is an Intrusion Test? A Guide for Australian Businesses
An intrusion test is an authorised, simulated attack on your organisation's systems, networks, or...
What is Endpoint Detection and Response?
Think of Endpoint Detection and Response (EDR) as an elite security detail for every single device...
As Australian businesses accelerate their move into the cloud, securing those digital environments has become a core business function, not just an IT task. With high-profile data breaches acting as a sharp reminder, CIOs and CISOs are rightly prioritising investment in robust cloud computing security services. This guide breaks down the essential services that form the foundation of a resilient Australian organisation.
The New Standard for Cloud Security in Australia

The rapid shift to cloud infrastructure is not just a trend; it is a fundamental change in how Australian organisations operate and compete. This migration, however, brings with it a new and complex set of security challenges that demand specialised expertise.
For many Australian IT leaders, the question is no longer if they should move to the cloud, but how to do it securely. Consequently, protecting data, applications, and infrastructure in these distributed environments requires a deliberate strategy, one that moves well beyond traditional, on-premises security thinking.
A Shared Security Partnership
At its heart, cloud security operates on a Shared Responsibility Model. This is a critical concept for any leader managing cloud assets. Think of it like owning a flat in a high-rise building.
The building owner—your cloud provider like AWS or Azure—is responsible for securing the physical building, its foundation, and common utilities. In the same way, they secure their global infrastructure, hardware, and the core services their cloud runs on.
You, however, are responsible for locking your own flat door, installing an alarm, and securing your valuables inside. In the cloud, this means you are responsible for securing your data, configuring access controls correctly, managing user permissions, and protecting your applications.
The core idea is that security is a partnership. While cloud providers offer a secure foundation, the ultimate responsibility for protecting what you put in the cloud rests with your organisation. Misconfigurations and poor access management remain the leading causes of cloud breaches.
The Financial Imperative for Strong Security
The push to strengthen cloud defences is clearly reflected in market forecasts. This parallel growth in spending highlights how intertwined cloud adoption and security investment have become.
Australian Cloud Adoption and Security Spending Forecast
This table highlights the parallel growth in public cloud spending and the necessary focus on security investments, providing a quick statistical overview of the market drivers.
| Cloud Service Category | Projected Spend (AU) | Year-over-Year Growth | Key Security Consideration |
|---|---|---|---|
| Infrastructure as a Service (IaaS) | A$10.2 billion | 22.5% | Misconfiguration and access control management. |
| Software as a Service (SaaS) | A$14.1 billion | 16.8% | Data protection, identity management, and vendor risk. |
| Total Public Cloud Services | A$31.6 billion | 18.8% | Integrating security across multiple provider platforms. |
Source: Adapted from industry forecasts for 2026.
This financial commitment underlines a critical insight for business leaders: cloud adoption and security investment are now inseparable. As organisations lean more heavily on IaaS and SaaS platforms, the need for effective cloud computing security services becomes urgent. You can read more about the Top Security Challenges in Cloud Computing to understand the motivations behind these measures.
This guide will demystify the services available, helping you make informed decisions to protect your digital assets and meet compliance obligations like the ASD Essential 8. Furthermore, you might find our guide on ASD cloud security implementation in Australia useful.
Understanding Your Cloud Security Service Options
Trying to get your head around the different cloud computing security services on offer can feel like a losing battle. Each service category, however, is designed to solve a specific business problem and add another layer of protection for your organisation’s data. Therefore, understanding what they do is the first step to building a security programme that actually works.
Let’s cut through the jargon. Think of your cloud environment as a large commercial building. You would not use the same security approach for the front lobby, the server room, and a rented office suite. Each part has different needs, and you need a specialised approach for each.
Securing the Building Blocks: IaaS, PaaS, and SaaS
Most cloud use falls into one of three models: Infrastructure as a Service (IaaS), Platform as a Service (PaaS), or Software as a Service (SaaS). Just as securing a building’s foundation is different from securing an individual flat, each model demands a different security focus.
-
IaaS Security (The Foundation and Structure): Here you rent the raw computing infrastructure—servers, storage, and networks. Securing IaaS is all about the fundamentals, like protecting the building’s core structure. Consequently, your main job is to prevent misconfigurations, control network traffic, and strictly manage who has the keys to the server rooms.
-
PaaS Security (The Workshops and Tools): With PaaS, you get a platform to build and run your applications without worrying about the underlying hardware. It is like renting a fully equipped workshop. Your security responsibility shifts to what you build and how you use the tools. Therefore, you need to secure your own applications and make sure no one leaves the workshop doors unlocked.
-
SaaS Security (The Individual Flats): SaaS gives you ready-to-use software like Microsoft 365 or Salesforce. This is like renting a fully furnished flat. Your security focus narrows to managing user access, protecting the data you put into the application, and ensuring the software itself is configured securely.
Managed Detection and Response (MDR)
Think of Managed Detection and Response (MDR) as your 24/7 security patrol, actively monitoring your entire cloud environment. This is not just a fancy alarm system. Instead, it is a team of human experts actively hunting for signs of trouble, investigating anything that looks suspicious, and responding fast to shut down breaches before they cause real damage.
For most Australian organisations, building an in-house, round-the-clock security operations centre is simply out of reach. MDR gives you access to elite threat hunters and advanced security technology as a service, letting you outsource this critical function. You can explore how this fits into a broader strategy in our guide on choosing the right MSSP security services.
Cloud-Native Application Protection Platform (CNAPP)
A Cloud-Native Application Protection Platform (CNAPP) is like having an integrated security and fire-suppression system designed and built into your cloud environment from day one. Instead of trying to bolt on different security tools after the fact—and hoping they work together—a CNAPP brings multiple security functions into one cohesive platform.
A CNAPP provides a ‘single pane of glass’ for your entire cloud environment. It brings together posture management, workload protection, and vulnerability scanning, giving your team complete visibility and control from development to production.
This integrated approach helps eliminate the security gaps that almost always appear when you stitch together separate tools, ensuring your applications are secure through their entire lifecycle.
Virtual CISO and Professional Services
Finally, a virtual CISO (vCISO) is your on-demand security strategist. If the other services are the guards and alarm systems, the vCISO is the expert who designs the building’s entire security blueprint, makes sure it meets all the compliance codes, and advises the board on risk.
This kind of service is invaluable for organisations that need high-level strategic guidance but do not need a full-time, in-house Chief Information Security Officer. A vCISO helps you align your security programme with business goals, manage compliance, and make commercially sound decisions.
The demand for this kind of expert-led service is one reason Australia’s managed security services market hit USD 1,115.3 million in 2025. It is part of a much bigger trend, with the local cloud market itself on track to reach USD 60,745.5 million by 2030. You can dig into these figures in Grand View Research’s Australian cloud computing outlook.
Aligning Security Services With Australian Compliance
For Australian organisations, cloud compliance is not just about ticking boxes. It is a commercial imperative. Getting it right proves to regulators, partners, and customers that your security is robust, turning a regulatory headache into a genuine business advantage.
The goal is not to buy a separate tool for every rule. Instead, it is about strategically using cloud security services to meet the core principles behind the standards. This ensures your security is not only compliant but also genuinely resilient. For Australian leaders, this alignment is the key to unlocking new markets and building lasting trust.
This diagram shows how different security services protect your cloud models (IaaS, PaaS, SaaS) and support your broader strategic goals.
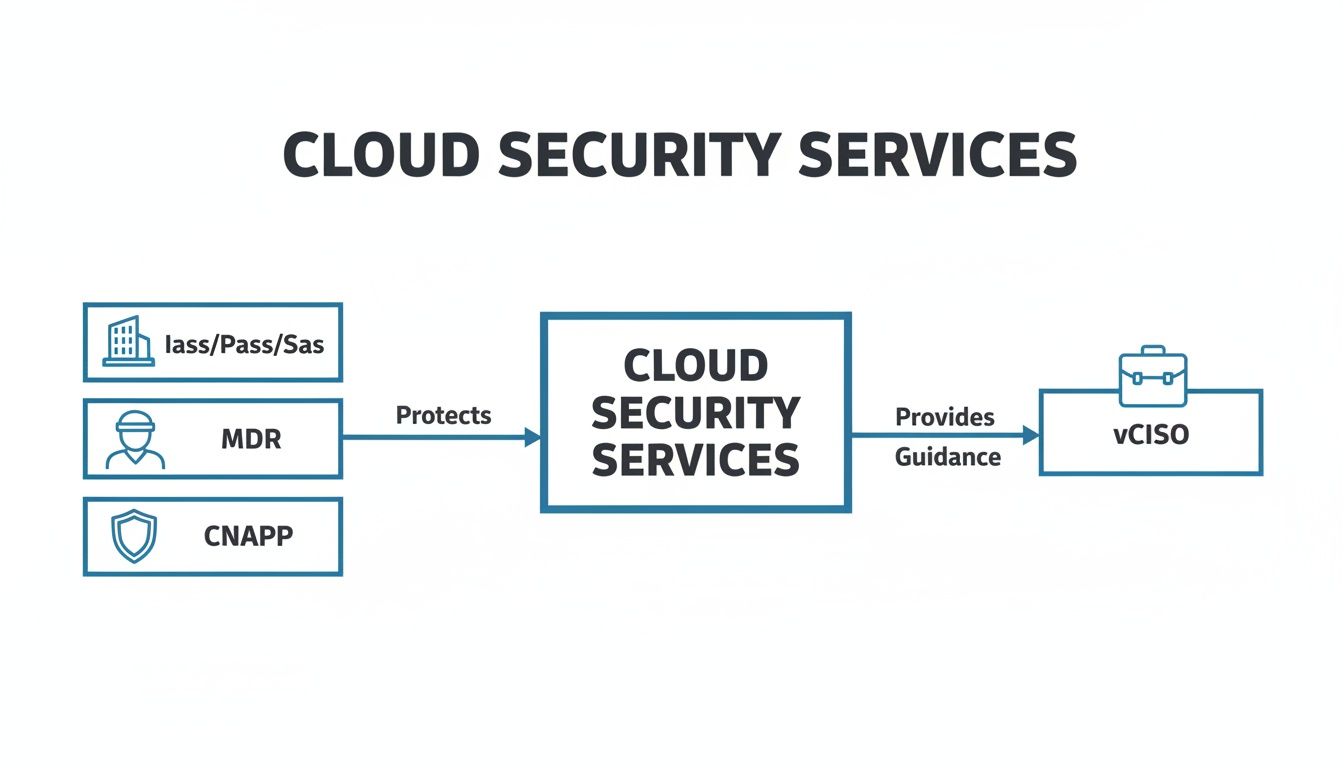
As you can see, securing the IaaS, PaaS, and SaaS layers is just the foundation. Advanced services like MDR, CNAPP, and vCISO provide the active defence and strategic oversight needed to run a mature and compliant security program.
Choosing the right service for a specific compliance need can feel overwhelming. The table below maps common Australian and global frameworks to the security services that directly address their core requirements.
Mapping Cloud Security Services to Compliance Needs
| Compliance Framework | Key Requirement Example | Primary Cloud Security Service | Supporting Service |
|---|---|---|---|
| IRAP / ASD Essential 8 | System Hardening & Incident Response | IaaS/PaaS Security | MDR for Cloud |
| ISO 27001 | Risk Assessment & Treatment | vCISO & Professional Services | Cloud Penetration Testing |
| SOC 2 | Continuous Security Monitoring | Cloud-Native Security Platform (CNAPP) | MDR for Cloud |
| PCI-DSS | Vulnerability Management & Segmentation | Managed Vulnerability Scanning | Cloud Network Security |
This mapping helps you move from abstract requirements to concrete actions. In short, it connects the “what” of compliance to the “how” of security services, making it easier to build a targeted and cost-effective strategy.
Meeting Government and Defence Standards
If you are aiming to work with Australian government agencies, compliance with the Information Security Registered Assessors Program (IRAP) and the Australian Signals Directorate’s (ASD) Essential Eight is non-negotiable. These frameworks demand a high level of verifiable security maturity.
To prepare effectively, it is worth understanding the full process of an information technology security audit, as this knowledge turns a compliance hurdle into a growth driver.
Key services that directly support these standards include:
- Cloud-Native Application Protection Platform (CNAPP): IRAP assessors need proof that controls are working continuously, not just at a point in time. A CNAPP delivers this by constantly scanning for misconfigurations and policy drift, providing the necessary evidence.
- IaaS/PaaS Security: A huge part of the Essential Eight focuses on hardening systems. Security services that automate IaaS and PaaS configuration against best-practice benchmarks are critical for preventing common breaches.
- Managed Detection and Response (MDR): The ability to detect and respond to threats in near real-time is a core government expectation. An MDR service provides the 24/7 monitoring and expert response needed to meet these stringent security demands.
Aligning With Global Frameworks Like ISO 27001 and SOC 2
As Australian businesses expand globally, proving compliance with international standards like ISO 27001 and SOC 2 becomes essential for winning enterprise deals. These frameworks are all about building and maintaining a complete Information Security Management System (ISMS).
A key takeaway here is that these standards are not one-off projects; they are continuous programs. Your cloud security services must support this ongoing cycle of risk assessment, control implementation, monitoring, and improvement.
Services that make this continuous compliance achievable include:
- vCISO Guidance: A virtual CISO is invaluable for developing the ISMS, defining its scope, running risk assessments, and preparing the organisation for audit. They provide the strategic leadership to navigate the complexities of these standards.
- Cloud Penetration Testing: Both frameworks require you to regularly test your security controls. Pen testing services find vulnerabilities in your cloud environment, giving you crucial evidence of due diligence for auditors.
Securing Cardholder Data for PCI-DSS
For any organisation that handles credit card data, Payment Card Industry Data Security Standard (PCI-DSS) compliance is mandatory. While the cloud adds new challenges, the right security services can make adherence much simpler.
Achieving this requires a targeted approach. You can read our detailed guide on PCI-DSS compliance requirements in Australia for more information.
Essential services for cloud-based PCI-DSS compliance include:
- Cloud-Specific Network Segmentation: Isolating your cardholder data environment (CDE) is a fundamental rule. Security services can help design and enforce strict segmentation using cloud-native tools, which minimises the scope and risk of your audit.
- Managed Vulnerability Management: PCI-DSS demands regular vulnerability scanning and fast remediation. A managed service ensures scans run consistently and that any findings are dealt with inside the required timeframes.
Selecting the Right Cloud Security Partner

Choosing a security partner is one of the most critical decisions any business can make. This is not just another procurement exercise; it is a direct investment in your organisation’s resilience. The right partner becomes a genuine extension of your team, shaping your ability to operate securely, meet compliance demands, and earn customer trust.
For Australian CIOs and IT leaders, the selection process must be tailored to your company’s size, maturity, and strategic goals. A one-size-fits-all approach simply does not cut it. You need a partner who understands your commercial reality and can deliver tangible value that goes well beyond the technology itself.
Criteria for SMEs and Scale-Ups
For small to medium-sized enterprises (SMEs) and fast-growing scale-ups, agility and cost-effectiveness are everything. The focus should be on finding a partner who understands the relentless pressure to move quickly without cutting corners on security fundamentals.
Key criteria here include:
- Fixed-Cost Engagements: Predictable pricing is non-negotiable for budgeting. Look for partners offering transparent, fixed-cost models for certifications and managed services, which takes the risk of scope creep and surprise invoices off the table.
- Rapid Certification Pathways: Time is money. A partner who specialises in accelerating compliance with frameworks like ISO 27001 or SOC 2 can give you a major competitive edge, helping you land those enterprise clients much faster.
- Seamless Tech Stack Integration: A good partner works with the tools you already have. They should have proven expertise in integrating their security solutions with your existing technology, especially cloud-native tools, to maximise your current investments.
Criteria for Large Enterprises
On the other hand, for large enterprises, the priorities pivot towards managing complexity, sophisticated threats, and strict regulatory oversight. Your ideal partner must bring deep expertise and the scale to handle multifaceted security challenges.
You should prioritise partners based on:
- Deep IRAP and Government Expertise: If you work with government agencies, proven experience with the IRAP assessment process and the ASD Essential Eight is a deal-breaker. The partner must be fluent in the nuances of government security standards.
- Proven Multi-Cloud Management: Enterprises rarely live in a single cloud. Your partner needs demonstrable capabilities in securing complex, multi-cloud environments (AWS, Azure, Google Cloud) with a single, unified strategy.
- Advanced Threat Intelligence: A mature security posture demands proactive threat hunting. Look for partners with a strong, Australia-centric threat intelligence capability that actively informs their detection and response work.
Choosing a partner is fundamentally about aligning capabilities with your business needs. For SMEs, it’s about speed and efficiency. For enterprises, it’s about managing complexity and deep-seated risk.
The Australian market for these specialised providers is expanding quickly. Australia’s managed security services market reached USD 1,115.3 million in 2025, fuelled by soaring demand for cloud computing security services. With the broader cloud market projected to hit USD 60.7 billion by 2030, this investment in security expertise is becoming a crucial differentiator, especially in regulated industries.
Crucial Questions for Potential Providers
To cut through the sales pitches, your due diligence needs to include some tough, insightful questions. These are the questions that reveal a provider’s true capability and whether they are a good cultural fit.
Consider asking things like:
- Team Background and Expertise: “Can you describe the specific backgrounds of the team members who will be assigned to our account? What are their certifications and hands-on experiences with frameworks relevant to our industry?”
- Automation vs. Human Expertise: “How do you balance automated tools with human analysis in your services, particularly in Managed Detection and Response? Can you walk me through a real-world example of how this collaboration works?”
- Demonstrating Return on Investment (ROI): “Beyond compliance certificates, how do you measure and report on the value you provide? How will you help us demonstrate a clear security ROI to our board?”
By asking these targeted questions, you shift the conversation from features to outcomes. This ensures you end up with a partner who is genuinely invested in your security success. You might also be interested in our deep dive into managed security services in Australia.
A Phased Roadmap to Continuous Cloud Defence

Trying to build a complete security program for your cloud environment all at once is a recipe for frustration. A better approach is to break the work into a logical, phased journey. This makes the project manageable and ensures each step you take builds on the last, strengthening your defences as you go.
This roadmap is not about a single, massive project. Instead, it is about shifting your organisation from a reactive, point-in-time security posture to one of continuous, proactive defence. The end game is to embed security so deeply into your operations that it becomes an always-on function.
Phase 1: Assessment and Strategy
You cannot plan a journey without knowing where you are and where you are going. The first and most critical phase is all about getting that clarity. Any security investment made without this foundation is just guesswork.
First, you should conduct a thorough cyber maturity assessment. This process benchmarks your current controls, processes, and technologies against a recognised framework, like the ASD Essential Eight or ISO 27001. The output is a clear, evidence-based list of your biggest risks and security gaps, telling you exactly where to focus first.
Next, you bring in a virtual CISO (vCISO) to help translate those findings into a workable plan. Your vCISO acts as a security north star, explaining technical risks in commercial terms to get board-level buy-in. They will help you build a multi-year security plan that lines up with your business goals, compliance needs, and budget.
Phase 2: Foundational Hardening
With a clear strategy in hand, phase two is all about building a strong defensive foundation. This is where you start fixing the fundamental weaknesses the assessment uncovered. The goal is simple: make your cloud environment a much harder target for attackers.
This involves a few key actions:
- Deploying Automated Controls: Wherever possible, you should implement automated security controls. For example, using tools to enforce secure IaaS configurations helps prevent the common, and costly, misconfigurations that lead to breaches.
- Optimising Native Security Tools: Many organisations already pay for powerful security tools inside their existing licences, like those within Microsoft Security. This phase focuses on properly configuring and tuning what you already own to maximise your ROI before buying anything new.
Essentially, this phase is about getting the basics right. By hardening your core infrastructure and making the most of what you have already got, you significantly raise your baseline security without necessarily making a huge new investment.
Foundational hardening is not a one-time task. It involves establishing a process of continuous configuration management and vulnerability scanning to ensure your environment remains secure as it evolves.
Phase 3: Proactive Defence
Once your foundational controls are solid, you can pivot from purely preventative measures to proactive defence. This phase is about actively hunting for threats that might have slipped past your initial defences and testing just how resilient your environment really is.
The centrepiece here is implementing Managed Detection and Response (MDR) for your cloud workloads. An MDR service brings a team of security experts to the table, providing 24/7 threat hunting to ensure suspicious activity is found and shut down before it becomes a major incident. This phase should also introduce automated penetration testing. These tools continuously simulate real-world attacks, allowing you to find and fix vulnerabilities as they appear, rather than waiting for an annual test.
Phase 4: Continuous Compliance and Resilience
The final phase locks in your security program, moving it to a state of continuous improvement and audit-readiness. The goal here is to maintain your security posture over the long term and make sure you can respond effectively when an incident eventually occurs.
This is built on two main pillars:
- GRC Platform Integration: Integrating your security controls with a Governance, Risk, and Compliance (GRC) platform gives you real-time visibility into your compliance status. It automates the painful process of collecting evidence for audits against frameworks like SOC 2 or IRAP.
- Incident Response Readiness: You will develop and test your incident response plan through tabletop exercises and practical simulations. This ensures your team knows exactly what to do in a crisis, which minimises damage and speeds up recovery time.
This phased approach ensures your investment in cloud computing security services is strategic and delivers compounding value over time. For a deeper look into structuring this journey, check out our guide on creating a cybersecurity roadmap for Australian organisations.
How Australian Industries Apply Cloud Security
It is one thing to talk about cloud computing security services in theory. It is another to see how they deliver real-world business value. Let’s look at three scenarios tailored to Australian organisations, moving beyond the abstract to show how strategic security investment drives growth and protects sensitive data.
These examples reflect the daily pressures Australian IT and risk leaders face. From securing venture capital to protecting patient records and fending off ransomware, the right security partnership turns compliance obligations and security threats into a genuine commercial advantage.
Scenario 1: FinTech Startup Securing Investment
A Sydney-based FinTech startup hit a common roadblock while trying to secure its first round of institutional funding. Potential enterprise clients and investors demanded both PCI-DSS and SOC 2 compliance before signing any contracts. Consequently, the startup needed to achieve certification rapidly and cost-effectively to keep its growth plans on track.
The solution involved a two-pronged approach:
- vCISO Strategy: First, they engaged a virtual CISO to develop a pragmatic, risk-based security roadmap. The vCISO translated the complex requirements of PCI-DSS and SOC 2 into an actionable project plan, providing board-level strategy without the expense of a full-time executive.
- Managed Compliance Services: Next, the startup used a managed compliance service to implement the necessary controls. This service used automated tooling to continuously monitor the cloud environment, gathering the evidence needed for a successful and swift audit.
By blending high-level strategy with efficient execution, the startup achieved both certifications in under six months. This did not just unlock the funding they needed; it became a key sales asset, proving a commitment to security that set them apart from their competitors.
Scenario 2: Healthcare Provider Protecting Patient Data
An established healthcare provider in Melbourne was migrating its patient record system to a hybrid cloud environment. The project’s success hinged on meeting strict data sovereignty requirements under Australian law and achieving ISO 27001 certification to assure patients and partners that their sensitive health information was safe.
The provider’s internal IT team partnered with a security specialist to navigate these complexities.
For healthcare organisations, data sovereignty is not just a compliance issue; it is a matter of public trust. The security strategy had to ensure all patient data remained within Australian shores while still making the most of the cloud’s scalability.
Their solution focused on two core elements:
- Managed Detection and Response (MDR): A 24/7 MDR service was deployed to monitor the new hybrid cloud for any signs of unauthorised access or suspicious activity. This provided the real-time threat detection essential for protecting high-value health records.
- Expert GRC Support: A Governance, Risk, and Compliance (GRC) team helped map the controls within the new cloud environment directly to ISO 27001 and local privacy laws, ensuring the migration was compliant from day one.
Scenario 3: Law Firm Defending Against Ransomware
A mid-market law firm in Brisbane, holding vast amounts of confidential client data, recognised its growing exposure to a ransomware attack. To strengthen its defences and align with client expectations, the firm decided to adopt the ASD Essential Eight maturity model as its security benchmark, with the primary goal of building a robust incident response capability.
The firm focused on foundational resilience, first engaging a partner for a cyber maturity assessment. This process quickly identified critical gaps in their incident response planning and endpoint security.
The resulting work focused on developing a practical incident response plan and running tabletop exercises. This ensured the legal team knew exactly what to do during a security crisis, significantly improving their ability to withstand and recover from a potential attack.
Frequently Asked Questions About Cloud Security
To wrap up, let’s tackle some of the most common questions Australian IT leaders ask about cloud computing security services. These answers pull together the key ideas from this guide into practical advice.
How do we manage security in a multi-cloud environment?
Managing security across AWS, Azure, and Google Cloud at the same time is a huge challenge. If you try to manage each one as a separate silo, you are guaranteed to create blind spots and apply policies inconsistently. Attackers look for exactly these kinds of gaps.
This is the problem a Cloud-Native Application Protection Platform (CNAPP) is built to solve. It gives you a single, unified view for visibility, compliance checks, and threat detection across your entire cloud footprint. Furthermore, partnering with a security provider who knows multi-cloud environments inside and out is essential to harmonise your controls and build a defence that actually works together.
Your objective should be to enforce a single, consistent security baseline everywhere, no matter which cloud provider you’re using. This approach massively simplifies management and cuts down the risk of a misconfiguration in one cloud environment compromising another.
What is the difference between a vCISO and a full-time CISO?
The main difference comes down to the delivery model and the cost. A vCISO (virtual Chief Information Security Officer) provides strategic cybersecurity leadership on a fractional, as-needed basis. It is a great model for organisations that need expert guidance for board reporting, compliance strategy, and risk management but cannot justify the high cost of a full-time executive salary.
A full-time CISO, on the other hand, is an employee who handles both the high-level strategy and the day-to-day running of the security team. For many mid-market Australian companies, a vCISO is the only practical way to get access to the top-tier strategic expertise that would otherwise be financially out of reach.
How can we justify the cost of cloud security to our board?
You need to frame the investment as a direct business enabler and a clear risk reduction activity, not just another technical expense. The best way to achieve this is by building a solid business case.
First, put a number on the potential financial damage of a data breach. That includes regulatory fines from bodies like the OAIC, the cost of incident response, operational downtime, and the long-term harm to your reputation. You can then contrast this potential six or seven-figure loss against the predictable, fixed cost of managed cloud computing security services.
Even better, show how strong security actually generates revenue. Gaining certifications like ISO 27001 or completing an IRAP assessment are not just costs. They are keys that unlock doors to major enterprise clients and valuable government contracts, delivering a clear and measurable return on your investment.
At CyberPulse, we partner with Australian organisations to build resilient, compliant, and commercially grounded security programs. Our experts help you navigate everything from IRAP and ISO 27001 certification to proactive threat defence. To move from periodic checks to a state of continuous, proactive defence, learn more at https://www.cyberpulse.com.au.
Browse to Read Our Most Recent Articles & Blogs
Subscribe for Early Access to Our Latest Articles & Resources
Connect with us on Social Media

