This article provides a guide to the SMB1001 framework. Cyber attacks now hit Australian...
A Guide to NIST Cybersecurity Framework Implementation
First Published:
Content Written For:
Small & Medium Businesses
Large Organisations & Infrastructure
Government
Read Similar Articles
How to defend against Infostealer Malware
Infostealer malware is not just another cyber threat. It is a silent data thief designed to...
What Is an Intrusion Test? A Guide for Australian Businesses
An intrusion test is an authorised, simulated attack on your organisation's systems, networks, or...
What is Endpoint Detection and Response?
Think of Endpoint Detection and Response (EDR) as an elite security detail for every single device...
Your Guide to a Resilient Information Security Policy
An information security policy is the foundational document that outlines your organisation’s...
Getting a NIST Cybersecurity Framework implementation right is a strategic project, not just a box-ticking exercise. For Australian CIOs and CISOs, it is about building stronger defences, creating a common language for risk conversations with the board, and achieving genuine cyber resilience. Therefore, a successful implementation provides a clear competitive advantage.
Starting Your NIST Implementation Journey
Kicking off a NIST CSF implementation is a cornerstone activity for any Australian organisation that is serious about managing digital risk. It gives you a structured, repeatable way to protect your critical assets. Furthermore, this approach has become even more relevant as the government and industry ramp up their focus on cyber resilience.
We have seen a significant uptick in framework adoption across Australia, driven by both regulatory nudges and a real desire for more robust security. As of 2026, 82 per cent of Australian government entities now have a formal cyber security strategy in place, up from 75 per cent last year. This is not just a public sector trend; consequently, it shows a national shift toward structured risk management that influences everyone.
The Five Core Functions of the Framework
At its heart, the NIST CSF is built around five key functions that work together continuously. These functions create a high-level lifecycle for managing cyber security risk. As a result, they give security professionals a shared vocabulary to discuss what they are doing—from the server room right up to the boardroom.
The core functions provide a simple, logical structure for organising your security activities. Here is a quick-reference table that breaks down what each function aims to achieve.
The 5 Core Functions of the NIST Cybersecurity Framework
| Function | Objective |
|---|---|
| Identify | Understand the cyber security risks to your systems, people, assets, data, and capabilities. |
| Protect | Put the right safeguards in place to ensure critical services are delivered and to limit the impact of an attack. |
| Detect | Develop and implement activities to spot the occurrence of a cyber security event in a timely manner. |
| Respond | Take the right actions after a security event is detected to contain its impact. |
| Recover | Plan for resilience and restore any capabilities or services that were impaired due to a cyber security incident. |
These functions are designed to be a continuous loop, not a one-off checklist. The process ensures your security posture keeps evolving to meet new threats and business changes.
This flow is what makes the framework so powerful. It is a constant cycle of improvement.
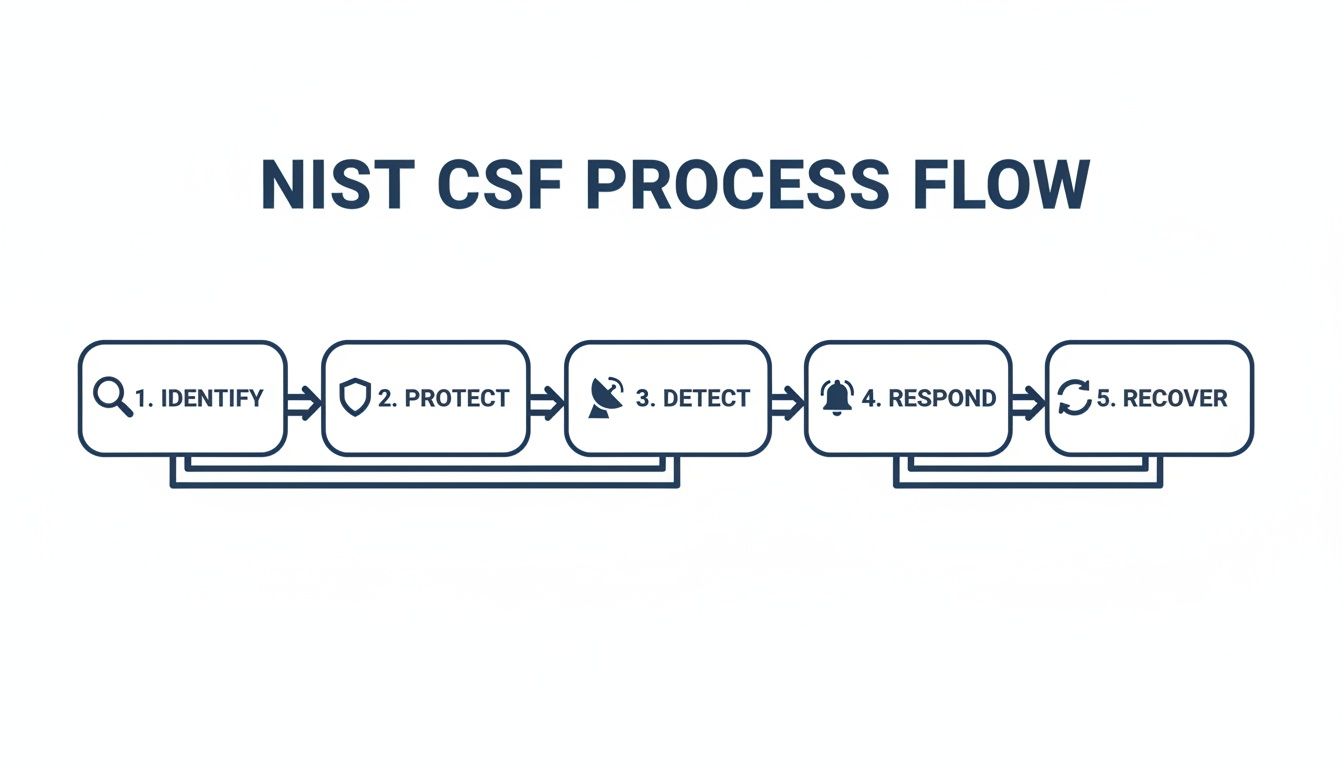
As you can see, the functions are not a linear checklist. Instead, they form an iterative loop, making sure your security program adapts as your business and the threat landscape change.
The real strength of the NIST CSF is its flexibility. It is a risk-based approach, not a rigid list of mandatory controls. This allows any organisation—from a small mid-market player to a large enterprise—to adapt it to their specific risk appetite, budget, and business goals.
Tiers and Profiles for Customisation
Beyond the core functions, the framework gives you two powerful tools to make it your own: Implementation Tiers and Profiles. These are what turn the CSF from a generic guide into a concrete action plan for your business.
Implementation Tiers are all about maturity. They help you understand how sophisticated your organisation’s risk management practices are, ranging from Tier 1 (Partial) to Tier 4 (Adaptive). Consequently, this gives you a clear benchmark to see where you stand and where you need to get to.
Profiles, on the other hand, help you map out the journey. First, you create a “Current Profile” to document where your security outcomes are today. Then, you define your goals in a “Target Profile”. The gap between those two profiles becomes your roadmap for improvement.
For a deeper dive into how these elements have evolved, check out our guide on the significant changes in NIST CSF 2.0.
Conducting a Thorough Gap Analysis for Your NIST Cybersecurity Framework Implementation
A successful NIST cybersecurity framework implementation starts with an honest, evidence-based look at your current security posture. You cannot chart a course to your destination without first knowing exactly where you are standing. This initial phase is all about getting a precise picture of what you have, what you need to protect, and where the shortfalls lie.
Before you can assess anything, you have to define the boundaries. Scoping is the critical first step that determines which systems, data, business processes, and third-party dependencies the framework will cover. For an Australian enterprise, this might include customer data platforms subject to the Privacy Act, critical operational technology in a manufacturing plant, or financial systems governed by APRA standards.
You need to ask some hard questions to get the scope right. What are the crown jewels of your organisation? Which business units or services would cause the most damage if they were disrupted? Identifying these critical components ensures your gap analysis is focused and delivers meaningful results, rather than trying to boil the ocean.

Uncovering Your Current State
Once your scope is defined, the real work begins. This involves methodically assessing your existing security controls against the NIST CSF’s Categories and Subcategories. This is not a theoretical exercise; it requires gathering tangible evidence.
To pull this off, most organisations use a mix of methods:
- Documentation Review: Systematically going through existing policies, procedures, network diagrams, and previous audit reports to understand your documented controls.
- Stakeholder Interviews: Speaking directly with system owners, IT staff, and business leaders to understand how controls actually operate, not just how they look on paper.
- Technical Assessments: Using tools like vulnerability scanners or configuration management databases to verify that technical controls are in place and working as intended.
The goal is to move beyond assumptions and establish a factual baseline. For instance, your policy might state that all critical servers are patched within 30 days, but a technical assessment might reveal that 20% of those assets are non-compliant because of operational constraints. This is exactly the kind of gap you need to find.
Gathering Actionable Intelligence
Gathering this information is part science, part art. I have found that structured workshops with key people from IT, security, legal, and the business units are incredibly effective. These sessions help build a shared understanding of risk and create consensus around the current state of security.
For example, a workshop might reveal that while the IT team has strong technical controls for data backup (a Protect function), the business continuity plan (a Recover function) has not been tested in over two years. This highlights a gap not in technology, but in process and preparedness.
A gap analysis is fundamentally a risk discovery process. Its output should not be a simple pass or fail grade, but a detailed, prioritised list of risks and control deficiencies that directly inform your action plan.
Your findings should be documented clearly, mapping each identified gap back to a specific NIST CSF Subcategory (e.g., PR.DS-1: Data-at-rest is protected). This creates a direct link between your current state and what the framework wants you to achieve. An integral part of this is knowing how to properly evaluate these findings, and our guide on how to conduct a thorough risk assessment provides more detail on this process.
Ultimately, a well-executed gap analysis provides the foundation for your entire NIST journey. It transforms the framework from an abstract standard into a practical tool for making informed, risk-based decisions about where to invest your time, budget, and resources for the biggest impact.
Using Tiers and Profiles to Prioritise Action

You have finished the gap analysis. Now you have an honest, evidence-based picture of where your security posture stands today. The next phase of your NIST cybersecurity framework implementation is all about turning those findings into a smart, strategic action plan. This is where the framework’s Tiers and Profiles become your most valuable tools for prioritising effort and, just as importantly, budget.
They help you tackle two critical questions: “How mature are our risk management processes, really?” and “What does ‘good’ actually look like for our organisation?” Consequently, answering these moves you from a daunting list of gaps to a focused roadmap that ties security improvements directly to your business goals and risk appetite.
Benchmarking Your Maturity with Implementation Tiers
Before you can plan the journey, you need to know your starting point. The NIST CSF offers four Implementation Tiers to help you benchmark your organisation’s high-level approach to managing cybersecurity risk. It is crucial to understand these are not just maturity levels. Instead, think of them as a way to describe how your organisation views and handles cyber risk.
It’s really a conversation starter for the leadership team about how integrated security truly is across the business.
- Tier 1: Partial
At this stage, risk management is often ad-hoc and reactive. Security practices are informal, applied inconsistently, and there is very little awareness of cyber risk at an organisational level. - Tier 2: Risk-Informed
Management has approved some risk management practices, but they might not be formal, organisation-wide policy. You have a decent grasp of your risk environment but probably struggle to execute consistently. - Tier 3: Repeatable
Your organisation has formal, board-approved risk management policies. Procedures are documented, updated regularly, and your people have the skills and knowledge to follow them. - Tier 4: Adaptive
Cybersecurity is part of your organisational DNA. You are actively adapting your practices based on lessons learned and predictive indicators, and you share threat intelligence with partners to improve collective security.
In my experience, most Australian mid-market organisations land somewhere between Tier 1 and Tier 2 when they first start. The key is to remember that reaching Tier 4 is not always the goal. It is about picking a Tier that makes sense for your business drivers, threat landscape, and compliance duties, like those under the SOCI Act.
Your target Tier needs to be a realistic ambition. A financial services firm handling sensitive customer data under APRA regulations will have a very different target than a small not-for-profit with a much lower risk profile. Being brutally honest in this self-assessment is the only way it works.
Defining Your Journey with Current and Target Profiles
With a Tier in mind, it is time to get granular with Profiles. A Profile is simply a snapshot of your cybersecurity outcomes, mapped against the CSF’s Functions, Categories, and Subcategories. The real magic happens when you create two of them.
First up is your Current Profile. This is where your gap analysis gets put to work. You go through the framework’s Subcategories and document your ‘as-is’ state, mapping your existing controls and their effectiveness. This creates a detailed inventory of what you are doing right now.
Next, and this is the most important part, you build your Target Profile. This is your ‘to-be’ state—a clear declaration of the security outcomes you want to achieve. This is not about ticking every box across all 100+ Subcategories. Instead, it is a deliberate, focused exercise in prioritisation.
For example, an Australian online retailer’s Target Profile would naturally prioritise Subcategories in the Protect Function related to payment card data (PR.DS-1, PR.DS-5) to meet its PCI DSS obligations. That same retailer might place a lower priority on certain physical access controls if its entire operation runs in the cloud.
This process ensures your resources are aimed where they will deliver the biggest risk reduction and business value. Building this Target Profile is a cornerstone of any practical cyber security strategy that aligns with your business goals. The difference between your Current and Target Profiles becomes your actionable roadmap—the guide for every decision you make in your NIST cybersecurity framework implementation.
Mapping Controls for Australian Compliance
Once you have settled on your Target Profile, it is time to get practical. This is where your NIST CSF strategy moves from the whiteboard into the real world. You will start selecting and mapping specific security controls to the outcomes you just defined. Do not mistake this for a simple box-ticking exercise; this is about building a single, cohesive security program that is both effective and efficient.
One of the NIST CSF’s best features is that it is not prescriptive. It does not hand you a rigid checklist of controls. Instead, it provides Informative References, which point to controls within other well-known standards. This flexibility is its greatest strength. It lets you use the CSF as a Rosetta Stone, translating your high-level risk goals into concrete actions using frameworks your team already knows.
For Australian organisations, this mapping is a game-changer. It is the key to avoiding the all-too-common “compliance fatigue” that sets in when you are juggling multiple, overlapping security requirements. Therefore, the goal is to create one integrated control set that satisfies several obligations at once.
Aligning NIST with Local Frameworks
The most crucial mapping exercise for any Australian business is aligning the NIST CSF with ISO 27001 and the Australian Signals Directorate’s (ASD) Essential Eight. These frameworks are the cornerstones of our local security landscape. Proving your alignment is something regulators, partners, and enterprise customers increasingly expect to see.
Let’s take a common example. A NIST Subcategory like PR.AC-1 (Identity and Access Management) maps directly to controls in both frameworks:
- ISO 27001: This clearly lines up with Annex A controls like A.5.15 (Access control) and A.5.16 (Identity management).
- ASD Essential Eight: It directly supports the principles of Restricting Administrative Privileges and Multi-Factor Authentication.
By drawing these lines, you can use your existing ISO 27001 certification or your work on the Essential Eight to prove you are meeting NIST outcomes—and the other way around. It creates a powerful synergy, turning what could be separate compliance activities into a single, unified defence strategy. For many Australian organisations, the easiest way to manage this is to build a compliance platform that can handle multiple frameworks.
The key is to think ‘implement once, comply many.’ By intelligently mapping NIST to ISO 27001 and the Essential Eight, you create a robust, defence-in-depth architecture that meets multiple requirements without tripling the workload. It is the most commercially grounded approach for any Australian CISO.
This table gives you a high-level look at how the main NIST CSF Functions connect with controls you are likely already familiar with from ISO 27001 and the Essential Eight.
NIST CSF Mapping to Common Australian Frameworks
| NIST CSF Function | Example ISO 27001:2022 Annex A Control | Related ASD Essential Eight Strategy |
|---|---|---|
| Identify | A.5.7 Threat intelligence | (Implicitly supports all strategies) |
| Protect | A.5.23 Information security for use of cloud services | Application control / Patch applications |
| Detect | A.8.16 Monitoring activities | (Underpins detection of failed controls) |
| Respond | A.5.26 Information security incident management response | (Follows detection of malicious activity) |
| Recover | A.5.30 ICT readiness for business continuity | Regular backups |
As you can see, the activities you undertake for one framework directly contribute to your maturity in others, making your overall compliance effort far more manageable.
Implementing Controls Across People, Process, and Technology
With your controls mapped out, implementation needs to hit all three pillars of a modern security program: people, process, and technology. If you neglect one area, the others will eventually fail. For instance, deploying a state-of-the-art endpoint protection tool (technology) offers little value if your team (people) is not trained (process) to spot a phishing email.
People
This is about more than just an annual, box-ticking security awareness course. It means fostering a genuine security-first culture where every single employee understands they have a role to play in defending the organisation.
Process
Here, the focus is on documenting and operationalising your controls. This is where you develop your formal incident response plan, establish a robust change management process, and define clear procedures for regular backups and, just as importantly, recovery tests. You can find excellent baseline procedures in documents like the Australian Government Information Security Manual (ISM).
Technology
Finally, you get to the tools. This is where you implement the technical safeguards themselves. It can be anything from foundational controls like firewalls and antivirus to more advanced solutions like Managed Detection and Response (MDR) services that give you 24/7 threat hunting and monitoring.
A balanced implementation across these three domains is what turns a collection of disparate security tools into a truly cohesive and resilient defence ecosystem.
Measuring Success and Driving Continuous Improvement
Getting the NIST Cybersecurity Framework implemented is not the finish line. It is the starting line for an ongoing commitment to resilience. A successful implementation shifts from a one-off project into a continuous program of measurement, refinement, and improvement. This is where you prove the value of your investment and move beyond initial setup to a state of proactive defence and perpetual audit readiness.
The core idea is simple: you cannot manage what you do not measure. After establishing your controls and bridging the gap between your Current and Target Profiles, you must define how you will track progress. This means developing meaningful metrics that show genuine risk reduction, not just activity.
Defining Meaningful Key Performance Indicators
To measure success, you need to move past vanity metrics. The number of blocked phishing emails or patched systems is interesting, but these figures lack context. Instead, your Key Performance Indicators (KPIs) should be directly tied to the desired outcomes in your Target Profile and reflect tangible business risk.
Effective KPIs answer critical questions for the board and leadership team. Are we getting faster at detecting threats? Are we reducing our attack surface? Are our most valuable assets better protected today than they were last quarter?
Consider focusing on outcome-driven metrics like these:
- Mean Time to Detect (MTTD): How long, on average, does it take for your security team to identify a security incident from the moment it begins? A decreasing MTTD is a strong indicator that your Detect capabilities are maturing.
- Mean Time to Respond (MTTR): Once detected, how quickly can you contain and neutralise a threat? This KPI directly measures the effectiveness of your Respond function.
- Percentage of Critical Assets with Patched Vulnerabilities: This metric moves beyond a simple patch count. Instead, it focuses on applying patches to the systems that matter most, demonstrating a risk-based approach to vulnerability management.
- User Phishing Simulation Click-Through Rate: This measures the effectiveness of your security awareness training. A downward trend shows your ‘human firewall’ is becoming stronger.
Your KPIs should tell a story about risk reduction. A CISO who can report a 20% reduction in MTTD over six months is providing the board with a far more compelling business case for security investment than one who simply reports that 5,000 viruses were blocked.
Establishing a Rhythm of Continuous Monitoring
The threat landscape does not stand still, and neither can your security posture. Continuous monitoring is the engine that drives ongoing improvement within the NIST CSF. This means shifting from periodic, point-in-time audits to a state of constant vigilance and assessment. This proactive stance is essential, particularly given the escalating threat environment in Australia.
For instance, recent trends show the critical need for robust frameworks. Between late 2024 and early 2025, Australia saw malicious cyber attacks climb by 41 per cent, while serious information leakage incidents nearly doubled. To counter this, defensive visibility has been boosted with the deployment of over 25,000 new host-based sensors, highlighting a national push toward proactive monitoring.
Establishing a rhythm for reviews is crucial. This could involve:
- Monthly Security Committee Meetings: Review KPIs, discuss recent incidents, and assess progress against the action plan.
- Quarterly Target Profile Reviews: Re-evaluate your Target Profile to ensure it still aligns with business goals and the current threat landscape.
- Annual Gap Analyses: Conduct a formal gap analysis each year to measure maturity growth and identify new areas for improvement.
This cycle of ‘measure, review, adapt’ ensures the framework remains a living, effective part of your operations. Furthermore, it embeds security into your organisational culture, making it a key component of your Governance, Risk, and Compliance (GRC) strategy. You can learn more about how this fits into a broader strategy by reading our insights on effective cyber security GRC.
Ultimately, this continuous loop transforms your organisation from being merely compliant to being genuinely secure and resilient.
Common Questions on NIST Implementation in Australia
As Australian organisations formalise their security programs, many IT and security leaders have practical questions about implementing the NIST Cybersecurity Framework. This section addresses the most frequent queries we see, offering clear answers to help you navigate the process.

Is the NIST Cybersecurity Framework Mandatory in Australia?
No, the NIST CSF is not broadly mandated by law for all private businesses in Australia. However, the government strongly encourages it as a best-practice standard for building cyber resilience.
Its status is quickly shifting from a voluntary guide to a de facto requirement for demonstrating due diligence.
For certain entities, the obligation is more direct. Organisations governed by the Security of Critical Infrastructure (SOCI) Act 2018 must implement a risk management program, and the NIST CSF is a recognised and well-trodden path to compliance.
We are also seeing industry regulators and supply chain partners increasingly demand evidence of a structured security program. Therefore, proactively adopting the NIST CSF positions your organisation to meet these expectations and prepares you for future regulatory changes.
How Long Does a NIST Implementation Usually Take?
The timeline for a NIST CSF implementation varies significantly based on your organisation’s size, complexity, and current security maturity. It is crucial to approach this as an ongoing program, not a finite project with a fixed end date.
Here is a general guide based on our experience:
- Mid-sized organisations with some existing controls can often establish a baseline and show tangible progress within three to six months.
- Larger enterprises, or those starting from a lower maturity level, should budget for a 12-month journey or longer to fully embed the framework.
The initial push focuses on establishing the foundation—the gap analysis, Target Profile, and action plan. The true value, however, comes from the continuous cycle of assessment and improvement.
A key mistake is viewing the initial implementation as the endpoint. The real work is in the ongoing maintenance, monitoring, and refinement of your controls. The goal is to build a living security program that evolves with your business and the threat landscape.
Can We Use NIST if We Are Already ISO 27001 Certified?
Absolutely. In fact, holding an ISO 27001 certification gives you a significant head start. The NIST CSF and ISO 27001 are highly complementary and work together to create a powerful security posture.
Think of it this way:
- ISO 27001 provides the ‘how’ by specifying requirements for a robust Information Security Management System (ISMS). It gives you the policies, procedures, and management system structure.
- The NIST CSF provides the ‘what’ with its flexible, risk-based framework of cybersecurity outcomes organised into the five core Functions.
If you already have a certified ISMS, your existing risk assessments, control documentation, and management reviews can be mapped directly to the NIST Functions. This mapping allows you to demonstrate alignment with NIST outcomes efficiently, creating a unified security program without duplicating effort.
How Much Does a NIST Implementation Cost?
The cost of a NIST CSF implementation is highly dependent on the gap between your Current and Target Profiles. The investment is not in the framework itself—which is free—but in the resources needed to remediate identified gaps.
Costs generally break down into these areas:
- Consulting and Advisory: Fees for external experts to guide the gap analysis, profile development, and overall strategy.
- Technology Investment: Costs for new tools or services, such as a Security Information and Event Management (SIEM) system, Managed Detection and Response (MDR) services, or enhanced endpoint protection.
- Personnel and Training: The cost of security awareness training for all staff and specialised upskilling for the IT and security teams.
- Audit and Attestation (Optional): While there is no official NIST ‘certification’, you might incur costs for third-party attestation to provide assurance to stakeholders.
A well-planned implementation prioritises spending based on risk reduction, ensuring your budget is allocated to the areas that deliver the most significant security uplift.
Ready to move from periodic checks to a state of continuous, proactive defence? The expert team at CyberPulse can help you implement the NIST Cybersecurity Framework to build genuine resilience, streamline compliance, and keep your organisation audit-ready. Learn more about our end-to-end Governance, Risk, and Compliance support at https://www.cyberpulse.com.au.
Browse to Read Our Most Recent Articles & Blogs
Subscribe for Early Access to Our Latest Articles & Resources
Connect with us on Social Media

