This article provides a guide to the SMB1001 framework. Cyber attacks now hit Australian...
What is Endpoint Detection and Response?
First Published:
Content Written For:
Small & Medium Businesses
Large Organisations & Infrastructure
Government
Read Similar Articles
How to defend against Infostealer Malware
Infostealer malware is not just another cyber threat. It is a silent data thief designed to...
A Guide to NIST Cybersecurity Framework Implementation
Getting a NIST Cybersecurity Framework implementation right is a strategic project, not just a...
What Is an Intrusion Test? A Guide for Australian Businesses
An intrusion test is an authorised, simulated attack on your organisation's systems, networks, or...
Your Guide to a Resilient Information Security Policy
An information security policy is the foundational document that outlines your organisation’s...
Think of Endpoint Detection and Response (EDR) as an elite security detail for every single device in your organisation—including laptops, servers, and mobiles. Unlike traditional antivirus that merely checks for known threats at the door, EDR actively patrols the premises. Furthermore, it watches all behaviour, investigates anything unusual, and stands ready to neutralise threats instantly. This guide explains what endpoint detection and response is and its strategic value for Australian organisations.
A Strategic Capability Beyond Technology
With today's distributed workforces, which are common across Australia, legacy antivirus tools no longer suffice. They operate on a 'blacklist' model, only stopping threats they already recognise. Consequently, this leaves a massive gap for modern attacks like ransomware and fileless malware, which are designed to look benign and slip past these simple checks.
This is where Endpoint Detection and Response becomes a core strategic capability. It works on the assumption that a breach is not a matter of 'if' but 'when', and therefore focuses on spotting malicious activity after it bypasses your first line of defence. In short, EDR gives you the deep visibility and control needed to see and stop attackers before they can steal data or encrypt your systems.
Core Functions of What is Endpoint Detection and Response
An EDR solution is built on several key functions that work together to provide robust protection. These pillars transform endpoint security from a passive gatekeeper into an active hunter.
| EDR Capability | Description | Business Outcome |
|---|---|---|
| Comprehensive Visibility | Continuously collects detailed telemetry from every endpoint, including process executions, registry changes, network connections, and user activity. | Creates a complete historical record for investigation, allowing security teams to understand exactly what happened during an incident. |
| Sophisticated Detection | Analyses telemetry in near real-time using behavioural analytics, machine learning, and threat intelligence to identify subtle signs of an attack. | Finds modern and previously unseen threats that traditional antivirus misses, thereby reducing dwell time for attackers. |
| Deep Investigation | Allows security teams to visualise the entire attack chain, from initial entry to lateral movement, providing full context for an incident. | Enables rapid and accurate incident scoping, ensuring the entire breach is understood and contained, not just a single symptom. |
| Rapid Response Actions | Empowers security teams to take immediate action, from automatically isolating a compromised machine to running expert-led remediation scripts. | Contains threats instantly to prevent spread across the network, minimising business disruption and financial damage. |
The growing reliance on these capabilities is clear. By 2026, Australia’s endpoint security market is projected to surpass US$452 million, driven by the pressure on security teams to protect endpoints in distributed environments.
EDR is not about building higher walls; it is about having unparalleled intelligence inside those walls. It provides the context and power to act decisively when a threat inevitably gets through, which is essential for any resilient security programme aligned with frameworks like the ASD Essential 8.
For a deeper dive into protecting your organisation’s devices, you might be interested in our comprehensive guide to endpoint security services. This shift to proactive defence is crucial for Australian leaders navigating an increasingly complex threat environment.
How EDR Technology Actually Works
To truly get your head around what endpoint detection and response is, you need to look past the definition and see how it works under the hood. Think of an EDR solution as a digital nervous system. It constantly collects information, senses disturbances, and reacts with incredible precision, turning endpoint security from a passive guard into an active, intelligent defender.
The whole process runs in a continuous loop. First, it starts with gathering a huge amount of data, then moves through analysis, investigation, and finally, a decisive response. This cycle ensures threats are not just blocked, but are properly understood and completely removed.
The diagram below shows the core functions that drive this process, from initial visibility right through to response.
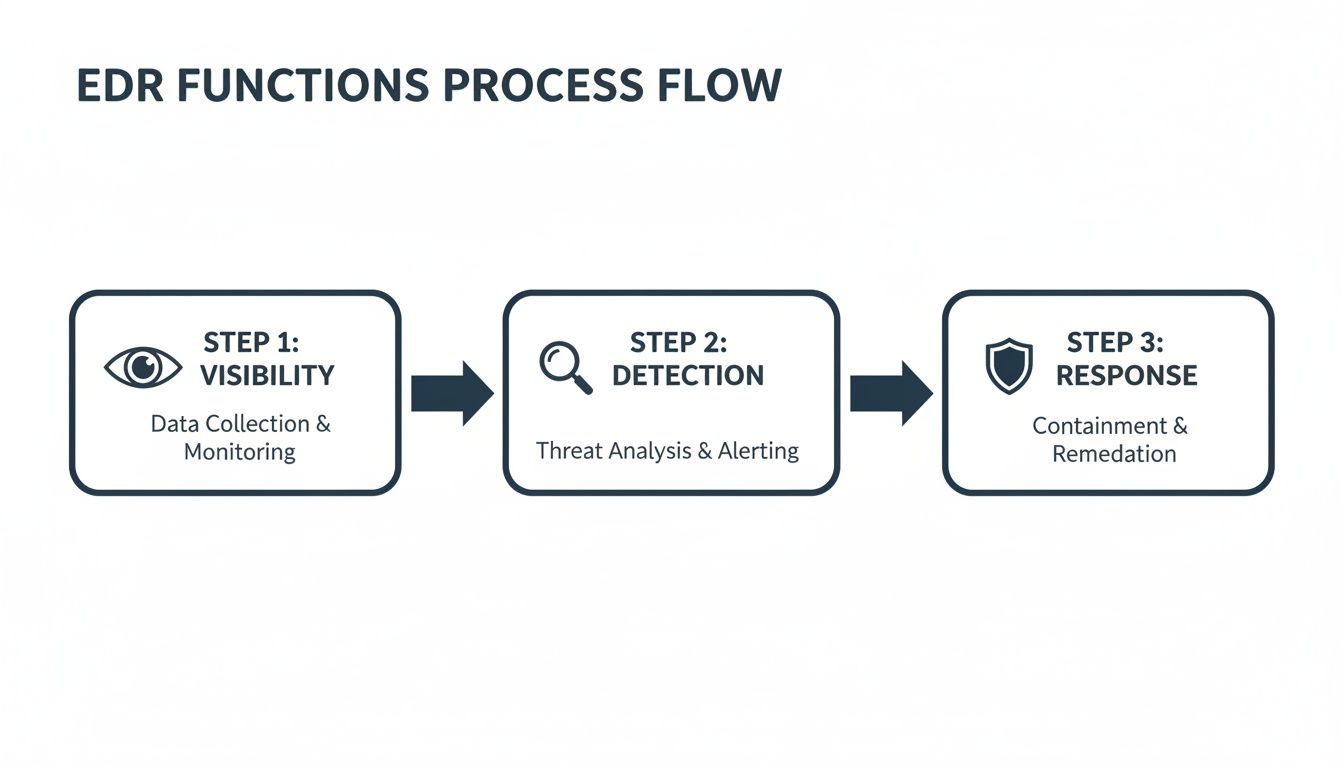
You can see how each stage builds on the last, creating a powerful system of non-stop monitoring and protection.
Step 1: Data Collection and Telemetry
The foundation of any good EDR platform is its ability to see everything happening on a device. It achieves this by deploying a lightweight software agent on every endpoint—laptops, servers, and even virtual machines. This agent acts like a sensor, continuously gathering a rich stream of data called telemetry.
This is not your basic logging. Instead, it is a detailed, moment-by-moment record of critical system activities. Some of the telemetry collected includes:
- Process Executions: What applications are running, their parent processes, and any command-line arguments used.
- Registry Modifications: Any changes made to the Windows Registry, a favourite hiding spot for malware trying to persist.
- Network Connections: All incoming and outgoing network traffic, including where it is going and how much data is being sent.
- File and Data Access: Which files are being created, modified, or deleted, and by what user or process.
This raw data is then securely streamed to a central analysis platform, usually in the cloud, where the real intelligence work begins.
Step 2: Real-Time Analysis and Detection
With a constant flow of telemetry coming in, the next step is to find the needle in the haystack—those subtle signs of malicious activity. EDR platforms use powerful techniques like behavioural analysis and real-time monitoring of everything happening on an endpoint to spot threats.
Unlike traditional antivirus that just looks for known virus signatures, EDR focuses on behaviour. It builds a baseline of what is normal for each device and then uses powerful analytics to spot anything out of the ordinary. For example, it might flag when a common program like Microsoft Word suddenly tries to encrypt files or connect to an unknown server—actions that are completely irregular and a strong sign of an attack.
EDR’s real power is its ability to connect seemingly unrelated events into a single story. A random registry change on its own might mean nothing. However, when it happens milliseconds after a suspicious network connection and a new process execution, it paints a clear picture of an attack in progress.
Step 3: Investigation and Threat Hunting
When an EDR platform detects a potential threat, it sends a high-quality alert to the security team. Crucially, it also provides all the surrounding data needed to investigate properly. Analysts can see the entire attack chain, often called a ‘process tree’, which lets them trace the incident right back to its root cause.
An analyst at a Sydney-based financial firm, for instance, could see that a malicious file came in via a phishing email, was opened by an employee, and then ran a PowerShell script to download ransomware. This forensic-level insight is vital for understanding the full scope of a breach and making sure every trace of the attacker is wiped clean. Many organisations rely on the expertise found within a Security Operations Centre to make the most of this capability.
Step 4: Automated and Guided Response
The final piece of the puzzle is taking action to contain the threat and get the endpoint back to a safe state. EDR gives security teams a range of response tools:
- Automated Containment: The system can automatically isolate a compromised device from the network, stopping a threat from spreading to other machines.
- Process Termination: Security teams can remotely kill any malicious processes running on an affected endpoint.
- File Remediation: The platform can quarantine or delete malicious files that were identified during the investigation.
- Guided Remediation: For more complex incidents, the EDR provides step-by-step guidance and tools to help analysts fully remove the threat and reverse its changes.
This combination of deep visibility, smart analysis, and fast response is what makes EDR a cornerstone of modern cyber defence for Australian organisations.
Comparing EDR, Antivirus, XDR, and MDR
Navigating the cybersecurity market can feel like swimming through an ocean of acronyms. For Australian leaders, telling the difference between Endpoint Detection and Response (EDR), Antivirus (AV), Extended Detection and Response (XDR), and Managed Detection and Response (MDR) is critical for making smart investments. Each plays a specific role, and understanding how they fit together is the key to building a credible defence.
Indeed, the whole conversation really starts with the fact that older, traditional tools can no longer keep up. Legacy antivirus is struggling against modern attack methods, creating a clear need for something more advanced.
Antivirus vs. EDR: A Fundamental Shift in Defence
Traditional antivirus software works like a bouncer at a nightclub with a specific list of known troublemakers. It scans files, looks for signatures of known malware, and blocks anything that is on the list. While it is still useful against common threats, it is completely blind to anything new or cleverly disguised, like fileless malware or zero-day exploits.
EDR, on the other hand, is like a dedicated security team watching every CCTV camera in the venue, all at once. It is not just checking IDs at the door; it is constantly monitoring for suspicious behaviour.
- Antivirus (AV): Focuses on prevention by blocking known malicious files. It asks, “Is this file on my blacklist?”
- EDR: Focuses on detection and response by analysing behaviour. It asks, “Is this process acting suspiciously, regardless of which file it came from?”
This behavioural approach is exactly why EDR has become a cornerstone of modern security. It can spot a legitimate program, like PowerShell, being used for malicious purposes—a tactic that would fly straight past traditional AV.
EDR vs. XDR: Expanding the Field of View
As an organisation’s technology footprint grows, security needs to see beyond just the endpoints. This is where Extended Detection and Response (XDR) comes into the picture. If EDR gives you deep visibility into your laptops and servers, XDR stitches that view together with everything else in your environment.
Think of EDR as high-definition cameras on every individual device. In contrast, XDR connects those cameras with others monitoring your network, your cloud apps (like Microsoft 365), and your email systems.
By correlating data from all these different sources, XDR can connect the dots of a complex attack. For instance, it could link a suspicious email (from email security), an unusual network connection (from network monitoring), and strange process activity (from EDR) into a single, unified incident. EDR is the essential foundation, but XDR provides the bigger picture.
EDR vs. MDR: The Critical Human Element
While EDR and XDR are powerful technologies, they are still just tools at the end of the day. They generate alerts and provide data, but they need skilled experts to interpret that information, investigate threats, and take decisive action. This is where Australia’s persistent cybersecurity skills shortage becomes a serious business risk.
This is the exact problem that Managed Detection and Response (MDR) is designed to solve.
- EDR is the technology: The advanced platform that gives you visibility and the ability to respond.
- MDR is the service: The 24/7 team of expert security analysts who operate that EDR technology for you.
An MDR service provides the human-led threat hunting, alert triage, investigation, and guided response needed to get the full value from an EDR investment. Without that expert oversight, EDR tools can create overwhelming alert fatigue for internal IT teams who are already stretched thin, which often leads to missed threats.
The growing demand for this service model is clear in market trends. In 2023, the Australian Endpoint Detection and Response (EDR) market was worth USD 76.0 million. By 2030, it is projected to climb to USD 501.0 million, growing at an impressive compound annual growth rate of 30.9%. While software sales led the market in 2023, the services segment is growing the fastest, directly addressing the skills gap in threat hunting and incident response. You can learn more about these Australian EDR market projections on grandviewresearch.com.
For many Australian organisations, an MDR partnership is the most practical way to get enterprise-grade security outcomes without the huge cost and difficulty of building a 24/7 in-house Security Operations Centre (SOC). To get a better feel for this model, take a look at our guide on what Managed Detection and Response is.
To help clarify these distinctions, the table below provides an at-a-glance comparison of each capability. It is designed to help Australian IT leaders quickly understand the different roles these solutions and services play in a modern security strategy.
EDR vs. Antivirus vs. XDR vs. MDR Key Differentiators
| Capability | Antivirus (AV) | Endpoint Detection & Response (EDR) | Extended Detection & Response (XDR) | Managed Detection & Response (MDR) |
|---|---|---|---|---|
| Primary Focus | Prevention of known malware | Detection and response to advanced threats on endpoints | Unified detection and response across multiple security layers | 24/7 security operations delivered as a service |
| Detection Method | Signature-based (known threats) | Behavioural analysis and threat intelligence (unknown threats) | Cross-domain correlation (endpoints, network, cloud, email) | Human-led threat hunting and analysis |
| Scope | Individual endpoints | Endpoints (laptops, servers, mobiles) | Endpoints, cloud, network, email, identity | The entire technology stack covered by the service |
| Response | Automated blocking and quarantine | Automated and analyst-driven containment and investigation | Coordinated response actions across the entire IT environment | Guided remediation and threat neutralisation by experts |
| Human Element | Minimal | Requires skilled security analysts to manage and investigate alerts | Requires a dedicated security team (SOC) to operate | A fully-staffed, 24/7 external SOC is provided |
| Best For | Basic protection against common malware | Organisations needing deep endpoint visibility and response capabilities | Mature organisations with a need to correlate threats across a complex IT ecosystem | Organisations without the in-house expertise or resources to run a 24/7 security operation |
Ultimately, choosing the right tool or service depends entirely on your organisation’s specific risk profile, existing capabilities, and strategic goals. While AV is a basic starting point, EDR, XDR, and MDR each solve progressively more complex security challenges that modern businesses face.
The Key Business Benefits of Implementing EDR
For Australian CIOs and CISOs, any technology investment must deliver clear commercial value. While Endpoint Detection and Response (EDR) is a powerful security tool, its real strength is how it turns technical features into tangible business outcomes. It helps shift security from being seen as a cost centre to a strategic enabler that directly protects revenue, reputation, and operational continuity.
Implementing EDR is not just about blocking more threats; it is about fundamentally changing how your organisation manages cyber risk. Indeed, it provides the visibility and control needed to build genuine resilience.

Reduce Attacker Dwell Time and Breach Costs
One of the most critical metrics in cybersecurity is attacker dwell time—the period between an attacker’s initial intrusion and their detection. The longer an attacker goes unnoticed, the more damage they can do, from stealing sensitive data to deploying ransomware across your entire network.
EDR drastically shrinks this window. By continuously monitoring for suspicious behaviour, it can spot the subtle signs of an attack that traditional tools miss.
- Rapid Detection: EDR identifies malicious activity in near real-time, meaning attackers have significantly less time to achieve their objectives.
- Automated Containment: The moment a threat is confirmed, EDR can automatically isolate the compromised endpoint from the network, preventing lateral movement and stopping a minor incident from becoming a major breach.
This rapid response directly reduces the financial and reputational fallout of a security incident. With the average cost of a data breach in Australia reaching millions, minimising dwell time offers a clear and compelling return on investment.
Enhance Security Team Efficiency
Australian organisations consistently face a significant cybersecurity skills shortage. Internal security teams are often stretched thin, spending too much time chasing down false positive alerts from legacy systems. EDR helps to alleviate this pressure by bringing focus and automation to their workflow.
Instead of drowning in low-quality alerts, an EDR platform provides high-fidelity, context-rich notifications. Consequently, this allows your team to focus their limited time and expertise on genuine threats that require human intervention.
By automating routine response actions, EDR frees up skilled security analysts from tedious, manual tasks. This empowers them to shift their focus to higher-value activities like proactive threat hunting, strategic planning, and improving the overall security posture.
Strengthen Incident Response and Forensics
When a security incident does occur, a swift and thorough response is critical for both operational recovery and regulatory compliance. EDR provides an invaluable, detailed record of everything that happened on a compromised endpoint, acting like a flight data recorder for your devices.
This granular visibility is essential for forensic investigations. Security teams can instantly trace the attack chain back to its root cause, understanding precisely which files were accessed, what data was exfiltrated, and which systems were affected.
This capability is not just a technical advantage; it is a business necessity. Having clear, detailed forensic data strengthens your formal incident response plan, demonstrates due diligence to regulators, and provides the board with confidence that the breach has been fully contained and remediated. Ultimately, it answers the crucial question, “What happened, and how do we ensure it never happens again?”
Integrating EDR into Your Cyber Resilience Strategy
Adopting Endpoint Detection and Response (EDR) is not just a software deployment; it is a strategic move that fundamentally strengthens your organisation’s cyber resilience. For Australian leaders, this means looking beyond technical features to see how EDR fits with your existing security programme, people, and processes. A successful rollout demands careful planning, with a sharp focus on business risk and regulatory alignment.
This process begins by tying your EDR implementation directly to local compliance frameworks. The most prominent of these is the Australian Signals Directorate’s (ASD) Essential Eight, which provides a practical baseline for building a robust security posture.
Aligning EDR with the Essential Eight
EDR is a powerful tool for achieving higher maturity levels across several Essential Eight controls. It delivers the deep visibility and response capabilities needed to not only implement these controls but also to prove their effectiveness to auditors.
Key areas where EDR provides direct support include:
- Preventing Malware Delivery and Execution: EDR’s behavioural analysis engine is highly effective at spotting and blocking malicious code, including novel strains that slip past traditional antivirus. This directly supports the controls designed to stop malware from running.
- Restricting Administrative Privileges: By monitoring all endpoint activity, EDR can detect unusual privilege escalation attempts or the misuse of admin accounts, providing a critical layer of oversight.
- Application Control: While EDR does not replace a dedicated application whitelisting solution, it provides vital visibility into what is actually running in your environment. This helps detect unauthorised software that could otherwise bypass your primary controls.
By mapping your EDR’s capabilities to these specific controls, you build a stronger business case for the investment and show a clear commitment to meeting Australian cybersecurity standards.
Creating a Phased Rollout Plan
Trying a ‘big bang’ deployment across your entire organisation often introduces unnecessary risk and complexity. Instead, a phased rollout plan allows your team to gain experience, refine processes, and demonstrate early wins. This approach ensures a smoother, more successful adoption.
A practical rollout could follow these stages:
- Identify Critical Assets: First, start with your most valuable systems—servers holding sensitive data, finance department workstations, or executive laptops. Securing these ‘crown jewels’ first delivers the greatest immediate risk reduction.
- Target High-Risk User Groups: Next, deploy the EDR agent to users who are frequently targeted by phishing or have elevated access, such as system administrators or developers.
- Broad Deployment and Tuning: Once the initial phases are stable, you can proceed with a broader rollout. During this stage, your team can fine-tune detection rules and response playbooks based on what you learned from the pilot groups.
Integrating with Your Existing Security Stack
An EDR solution should never operate in a silo. Its true value is unlocked when it integrates seamlessly with your other security tools, creating a unified defence ecosystem. Key integration points include your Security Information and Event Management (SIEM) and Security Orchestration, Automation, and Response (SOAR) platforms.
When EDR feeds its high-quality, contextual alerts into your SIEM, it enriches the data from your other tools, like firewalls and email gateways. This allows your security team to see the bigger picture and connect seemingly isolated events into a coherent attack narrative, thereby accelerating investigation and response.
This integration is fundamental to building a mature security operation. For a deeper understanding of how managed services can bring these elements together, you can learn more about the role of a Managed SOC and MDR.
How to Choose the Right EDR Solution
Picking the right Endpoint Detection and Response (EDR) solution is a make-or-break decision for any Australian organisation. The market is crowded, and the wrong choice can leave you with serious security gaps or bury your team in an avalanche of meaningless alerts. A structured evaluation is the only way to make sure the technology you choose fits your risk profile, operational capacity, and security goals.
This process needs to go well beyond a simple feature list. It is about a deep dive into technical capabilities, the impact on your day-to-day operations, and whether the vendor can actually support your business when it counts. By asking the right questions, you can cut through the marketing hype and find a solution that genuinely strengthens your cyber resilience.

Technical Capabilities Evaluation
At its core, an EDR platform has to be good at one thing: finding and stopping threats. Your evaluation should put these functions to the test using real-world attack scenarios that are relevant to your industry.
Here is what to look for:
- Detection Methodologies: Does the solution go beyond basic behavioural analysis? You need a combination of machine learning, AI-driven analytics, and high-quality threat intelligence to catch novel threats and keep false positives to a minimum.
- MITRE ATT&CK Framework Alignment: This is a non-negotiable benchmark for any modern security tool. The EDR platform must map attacker techniques and tactics back to the ATT&CK framework. This proves the vendor has a mature understanding of how adversaries operate.
- Response Actions: Check the range and flexibility of its response options. The tool must support automated actions, like isolating an endpoint, but also allow for precise, analyst-driven responses to handle complex incidents.
Operational Considerations
An EDR tool is only useful if it slots neatly into your daily security operations. A technically brilliant solution that your team finds impossible to manage is just a failed investment.
The best EDR platform delivers maximum security impact with a minimal performance footprint. Focus on how the solution will affect your endpoints and your security team’s workflow—that is what determines long-term success and return on investment.
Think about these operational factors:
- Agent Performance: The EDR agent has to be lightweight. It cannot slow down your endpoints. Running a proof-of-concept (POC) on a representative sample of your devices is the only way to validate this.
- Console Usability: Is the management console intuitive? Your security team should be able to investigate alerts, trace attack chains, and execute responses quickly, without needing weeks of training. A clunky or confusing interface will always slow you down.
Vendor and Partner Evaluation
Finally, look beyond the tech and at the company behind it. Strong local support and deep expertise are vital, especially during a security incident when every second counts.
Key things to evaluate here include:
- Local Australian Support: Does the vendor or their partner have a real presence in Australia? You need 24/7 support from a team that understands the local threat landscape and regulatory environment.
- Threat Intelligence Quality: Where does their threat intelligence come from? Dig into the quality, relevance, and timeliness of their intelligence feeds.
- Managed Services Availability: Given Australia’s cyber skills shortage, it is worth checking if the vendor offers a managed service (MDR). This can provide a pathway to expert 24/7 monitoring and response, which is critical for organisations that do not have their own Security Operations Centre.
By systematically working through these areas, you can confidently choose an EDR solution that delivers genuine protection. For more insights on this topic, you can explore our overview of endpoint security solutions and EDR.
Frequently Asked Questions About EDR
We get a lot of questions from Australian leaders trying to get their heads around Endpoint Detection and Response. Here are some of the most common ones we hear, with practical answers to help guide your strategy.
Can EDR Replace Our Existing Antivirus Software?
This is probably the most common question we get asked. The short answer is yes, in many cases it can. Most modern EDR platforms include what is known as Next-Generation Antivirus (NGAV), which is designed to replace traditional, signature-based AV.
However, some organisations still choose to layer EDR with their existing AV for a defence-in-depth approach. The real power of Endpoint Detection and Response is its ability to spot advanced threats based on their behaviour—the kind of activity that old-school AV almost always misses. Ultimately, whether you replace your AV depends on the features of your chosen EDR platform and your organisation’s appetite for risk.
How Much Performance Impact Does an EDR Agent Have on Endpoints?
It is a fair question. No one wants to roll out a security tool that grinds employee laptops to a halt. Thankfully, modern, cloud-native EDR agents are built to be incredibly lightweight.
The heavy lifting—all the data processing and threat analysis—happens in the cloud, not on the user’s machine. This means the performance hit on the actual endpoint is usually minimal. That said, performance can vary between vendors, so it is always smart to run a proof-of-concept (POC) on a sample of your devices to measure the impact for yourself before committing.
Is EDR Enough to Comply with the ASD Essential Eight?
While EDR is a massive help, it is not a silver bullet for Essential Eight compliance. It is a powerful tool that directly supports several of the key controls, especially those for preventing malicious code execution, and it is essential for reaching higher maturity levels.
But achieving full compliance requires a broader strategy. You still need solid application control, consistent patch management, and tight access controls. Think of EDR as the cornerstone of your compliance programme—it gives you the visibility and response capabilities you need to implement and prove that many of those other controls are actually working.
Strengthen your cyber resilience with a security partner that understands the Australian landscape. CyberPulse provides expert-led managed detection and response services that turn your EDR investment into a proactive, 24/7 defence. Learn how our ex-CISO specialists can protect your organisation.
Browse to Read Our Most Recent Articles & Blogs
Subscribe for Early Access to Our Latest Articles & Resources
Connect with us on Social Media

